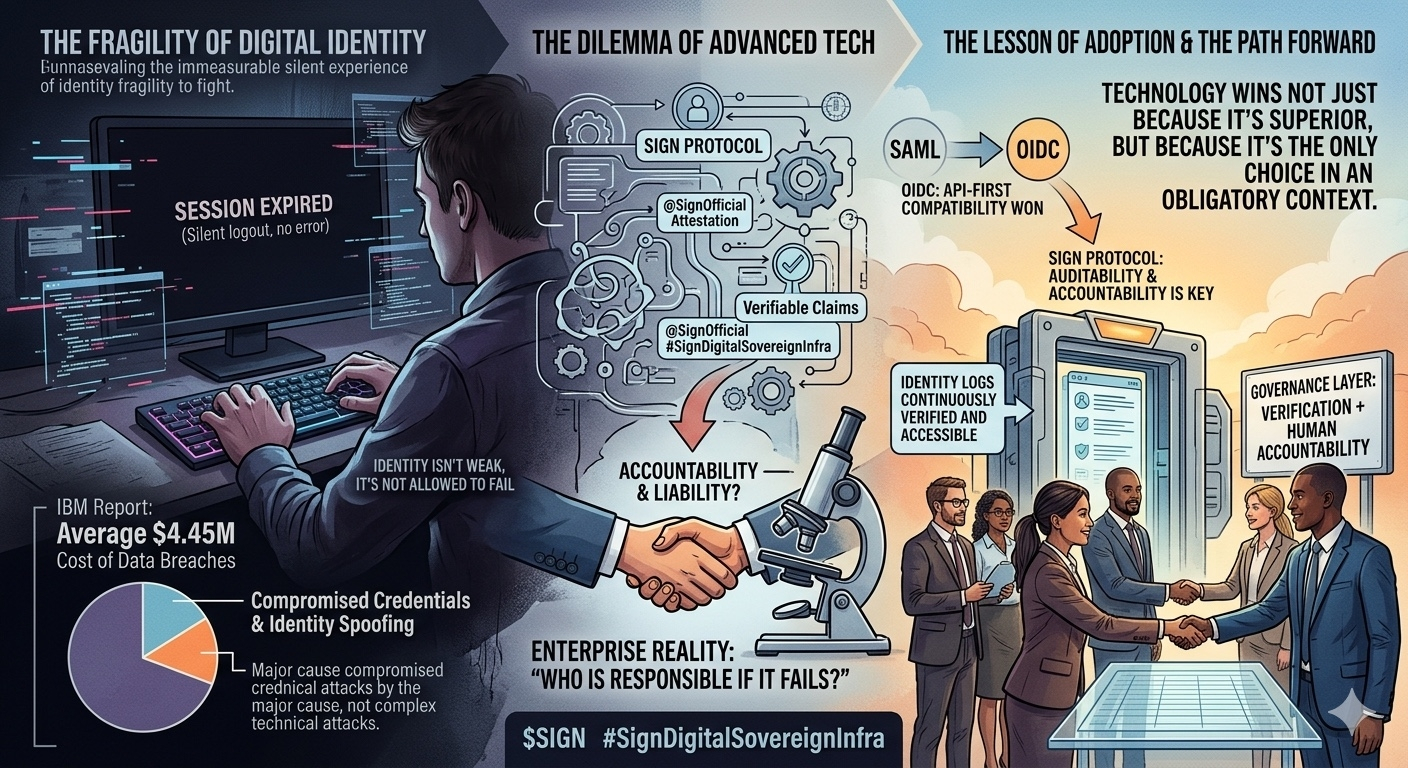
Do you understand the feeling of working while the application automatically logs out without any error message, nor any signs of response from the system? I have experienced this many times; the event unfolds silently but forces me to stop and think.
That moment made me realize one thing: Identity is inherently fragile. We often only pay attention to security when there is a major incident, but in reality, it is these small, quiet experiences that truly reflect the nature of the connection between users and the system.
When exploring @SignOfficial , my initial feeling was one of familiarity mixed with chaotic thoughts. Concepts like "attestation" or "verifiable claims" sound too foreign to end users and are heavily inclined towards infrastructure technology.
However, after delving into its structure, I find that this solution set is not lacking in terms of technology. But the problem is that businesses do not operate based on whether that technology is good enough or not. They have much more practical measurements.
I once read a report from IBM on the damages from data breaches. The average figure of over $4 million per incident does not surprise me as much as the core reason: Most do not come from complex attack techniques, but from credential leaks or identity fraud.
This leads to a reverse thought: Identity is not the weakest link because it is flawed, but because it is the part that is not allowed to fail. In system governance, once the front door is opened to the wrong person, all internal security layers become meaningless.
If we place Sign Protocol alongside solutions like Okta or Entra ID, we will see a significant gap in thinking. Decentralized technology promises transparency and independence, but businesses pose a more pragmatic question: "If a mistake occurs, who will resolve it?"
In the Enterprise environment, the ability to assign responsibility is just as important as security. A system without a clearly defined legal entity responsible will find it very difficult to receive approval for implementation.
Lessons from the technology shift
Looking back at the transition from SAML to OIDC, I noticed that OIDC prevailed not necessarily because it is absolutely more secure, but because it aligns better with the API-first trend. It wins because it "fits" with the flow of the era.

Sign Protocol seems to be facing a similar challenge. Its design is very precise, but it appears to be arriving before the market is ready. Companies often prioritize smaller, more certain steps over a complete leap that changes the system's nature.
I believe that technology does not win just because it is superior, but because it becomes the only option in a mandatory circumstance. With Identity, the ability to audit is the key. A distorted log can leave long-lasting consequences.
Businesses not only need a good authentication system; they need a system that is accountable. Sign Protocol is focusing on solving the authentication layer, while the true pain point for businesses lies in governance and human responsibility.
Microsoft once reported that the vast majority of attacks still exploit vulnerabilities from personal identification rather than coding errors. This shows the disconnect between technology efforts and operational reality.
I do not think Sign Protocol is going in the wrong direction; it just has not found the right falling point in the current binding ecosystem. Perhaps it will have to wait until an innovation begins, or new legal regulations force old standards to step back, for such transparent solutions to truly have a place. In the governance world, compulsion always carries more weight than mere superiority.
$SIGN #SignDigitalSovereignInfra