These past few days, I helped my cousin who just graduated find a house, and she has been tormented by various fake listings, unscrupulous agents, and unreliable subletters. To prove she is a 'high-quality tenant', my cousin was even forced to submit her salary statements from the past six months and detailed identity information to the agent.
This matter deeply moved me. We shout 'Code is Law' and 'decentralization' in Web3 every day, studying cross-chain protocols worth hundreds of millions of dollars, but once we return to the real 'stranger society', we still endure huge trust friction and privacy leakage risks in the most basic aspects of renting, dating, and making friends.
With this pain point, I have re-analyzed the white paper of \u003cm-89/\u003e word by word. I was amazed to find that people have previously regarded it as a token issuance tool or a grand sovereign infrastructure, which is truly too narrow. The underlying logic of SIGN can completely become the ultimate weapon to reshape our daily social trust.
Today, Moon will use plain language to break down the hardcore technology in the SIGN white paper and see how it helps us "avoid pitfalls" in real life.

1. Tear off the obscure label: What exactly is SIGN?
In the SIGN white paper, the core protocol is called Sign Protocol. It runs not only on EVM chains but also interconnects with various heterogeneous chains like Solana.
If we translate its operating mechanism into human language, it is essentially a "globally applicable, extremely flexible digital notary office." It consists of two core components:
1. Schema (data model template): Just like various "blank forms" at a notary office. You can define any form, such as "Tenant Asset Verification Form," "Real Education Verification Form," or "Single Status Declaration Form."
2. Attestation (cryptographic certificate): When you fill out the form and have it verified by an authoritative node (like a cooperating bank, school, or DAO organization), a stamped "certificate" will be generated on the chain.
This certificate is immutable and follows your wallet address, no longer being held hostage by any centralized app (like a local app or a matchmaking app).
2. Downward Attack: Reshaping Renting and Dating with SIGN
Understanding the principle, let's take a look at its destructive power in reality:
• Scenario 1: Renting (Saying Goodbye to Privacy Exposure)
In the past, when renting, landlords feared you would not pay rent, and you feared the landlord was a scammer. In the future, landlords can present a "Property Ownership Attestation" certified by housing authority nodes on SIGN; meanwhile, you no longer need to provide bank statements.
The white paper specifically mentions that SIGN is compatible with ZK (zero-knowledge proof) technology. This means that you can present a cryptographic certificate to the landlord through the protocol: "I prove that my monthly income is more than three times the rent," but the landlord absolutely cannot see what your specific salary is or which company you work for. Trust is established, and privacy is maintained.
• Scenario 2: Dating and Friendship (Ending the "Pig Butchering" Scam)
In today's social software, everyone has a Ferrari, and fake socialites and pig butchering scams are rampant. What would happen if social applications integrated the SIGN protocol?
Your homepage can host various on-chain certificates: your education Attestation, your real on-chain asset activity Attestation, and even your contribution certificate for participating in a certain public welfare DAO. These certificates are not self-edited images, but are verified by multiple parties across the internet. This is equivalent to creating a socially credible "business card" for you in the virtual world.
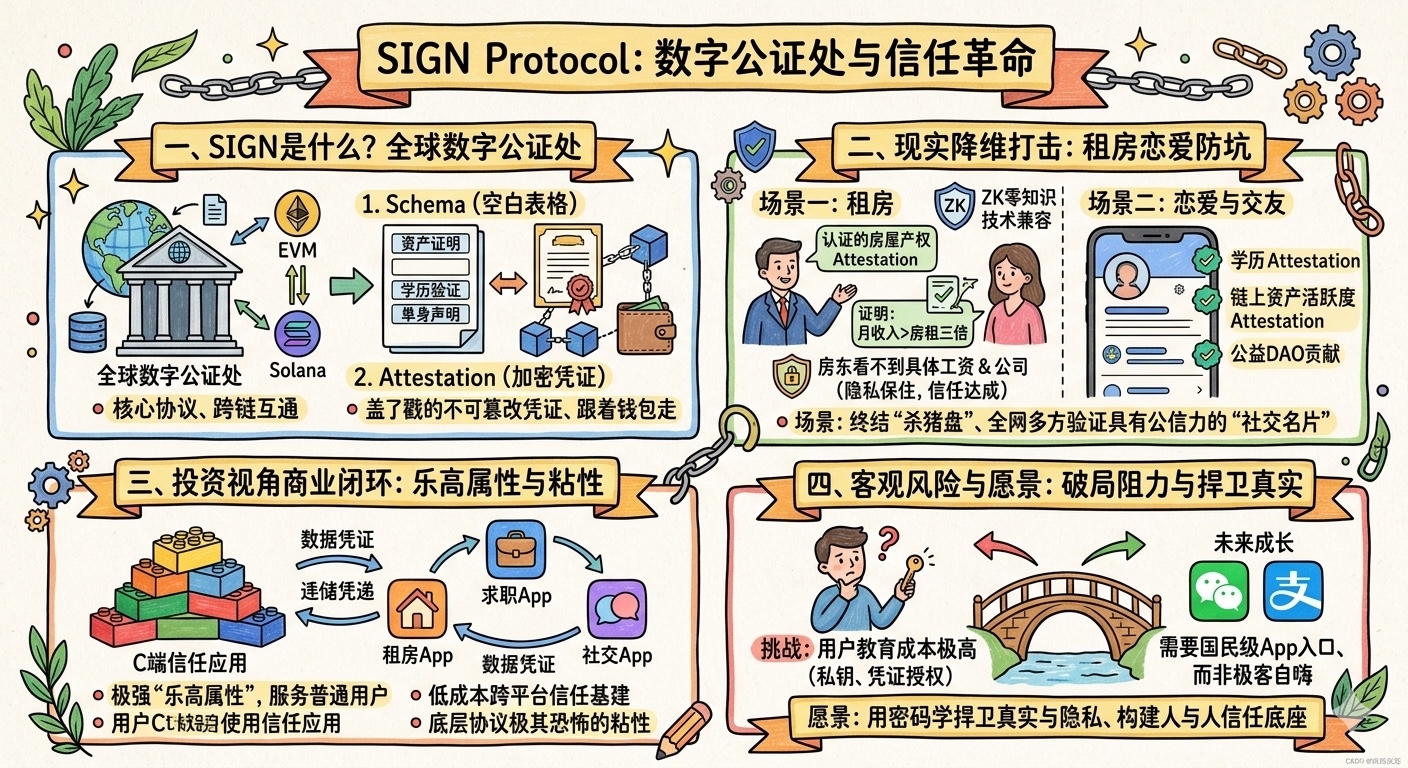
3. A Re-examination from the Investment Perspective: High-frequency "Low-dimensional Essential Needs"
Moon believes that when looking at a project, one cannot just focus on the story; the business closed loop must be considered.
In the past, we believed that SIGN's barrier lay in serving large organizations. However, from the architecture of the white paper, it has a very strong "Lego property," allowing any developer to create trust applications aimed at the C end (ordinary users) based on the Sign Protocol.
Traditional background check companies and intermediary platforms essentially earn money from "information asymmetry." SIGN provides a set of cost-effective, cross-platform interoperable trust infrastructure. When your credit certificate can seamlessly travel between rental apps, job-seeking apps, and social apps, the stickiness of this underlying protocol is extremely daunting.
4. Objective Minefield: Breaking the Pain Period of Habit
Of course, investment research cannot just report good news without addressing concerns. Although SIGN perfectly fits the trust pain points of a "stranger society" in technical logic, its implementation faces a huge barrier: user education costs.
There is still a long way to go for ordinary people to learn how to manage private keys and understand "certificate authorization." This requires the SIGN ecosystem to grow national-level applications with exceptional experiences, like WeChat and Alipay, as frontend entry points; otherwise, no matter how good the underlying protocol is, it can only be a self-indulgence of geeks.
But in any case, when we are engulfed by the ubiquitous "trust crisis" in real life, \u003cc-14/\u003e indeed provides us with an excellent solution to defend reality and privacy with cryptography. Understanding its potential in building the foundation of trust between people, you will realize the true terrifying aspect of this protocol.
Freelance writer: Moon
\u003ct-61/\u003e
