In many digital systems today, data often changes hands without truly being felt. Users provide information, then the system stores it, processes it, and in many cases shares it without further involvement from the data owner. This pattern has become so common that it is rarely questioned.
However, the direction that is starting to be seen in the development of Midnight is actually moving away from that pattern.
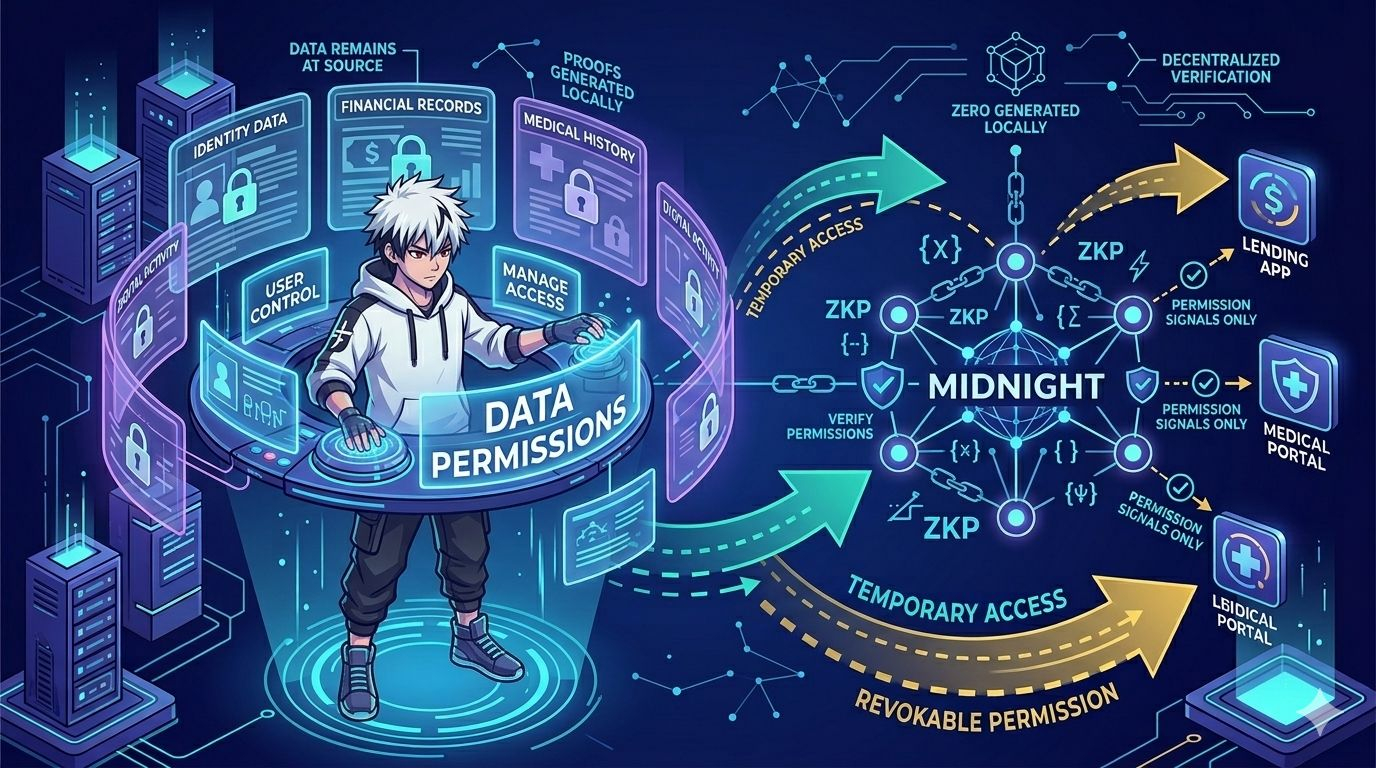
In the latest update, the concept of permission-based data has started to be increasingly emphasized, where every access to information not only depends on the system but also on the approval that can be directly controlled by the user. This is not just an additional feature, but part of an architecture designed from the start.
Interestingly, this permission is not static. Users do not just grant access once, but can reset, limit, or even revoke these permissions at any time. In some recent tests, this system has started to show how data can be 'borrowed' for specific purposes without actually being transferred or copied to another party.
This approach creates a new dynamic in digital interactions. Data is no longer considered something that is surrendered, but rather something that remains owned, with access granted only temporarily and in a controlled manner.
On the technical side, this mechanism is supported by a cryptographic proof system that ensures that access indeed occurs according to the permissions granted. Even when data never leaves its source, the system can still prove that the information has been used legitimately.
In practice, this model begins to open up possibilities for various new scenarios, especially in the context of digital identity and data-based services. Users can interact with the system without having to surrender all their information, only providing relevant proof as needed.
@MidnightNetwork #night $NIGHT


