i have a colleague who spent three years trying to make money by trading BITCOIN and ETHEREUM building permissioned blockchain systems for financial institutions and honestly the first thing she said when i described the SIGN CBDC namespace architecture was "that is a very confident design decision" 😂
i have been sitting with that reaction for the past two days trying to figure out exactly what she meant. and the more i read through the Hyperledger Fabric X implementation the more i think she was pointing at something real.
What the architecture is actually doing:
the SIGN private CBDC infrastructure runs on a single-channel architecture with namespace partitioning. that decision deserves more attention than it usually gets.
traditional Fabric deployments isolate different operations by creating separate channels. a channel is essentially a private subnet with its own ledger, its own membership, its own transaction flow. the privacy guarantee comes from the fact that participants on one channel have no visibility into what happens on another channel at all.
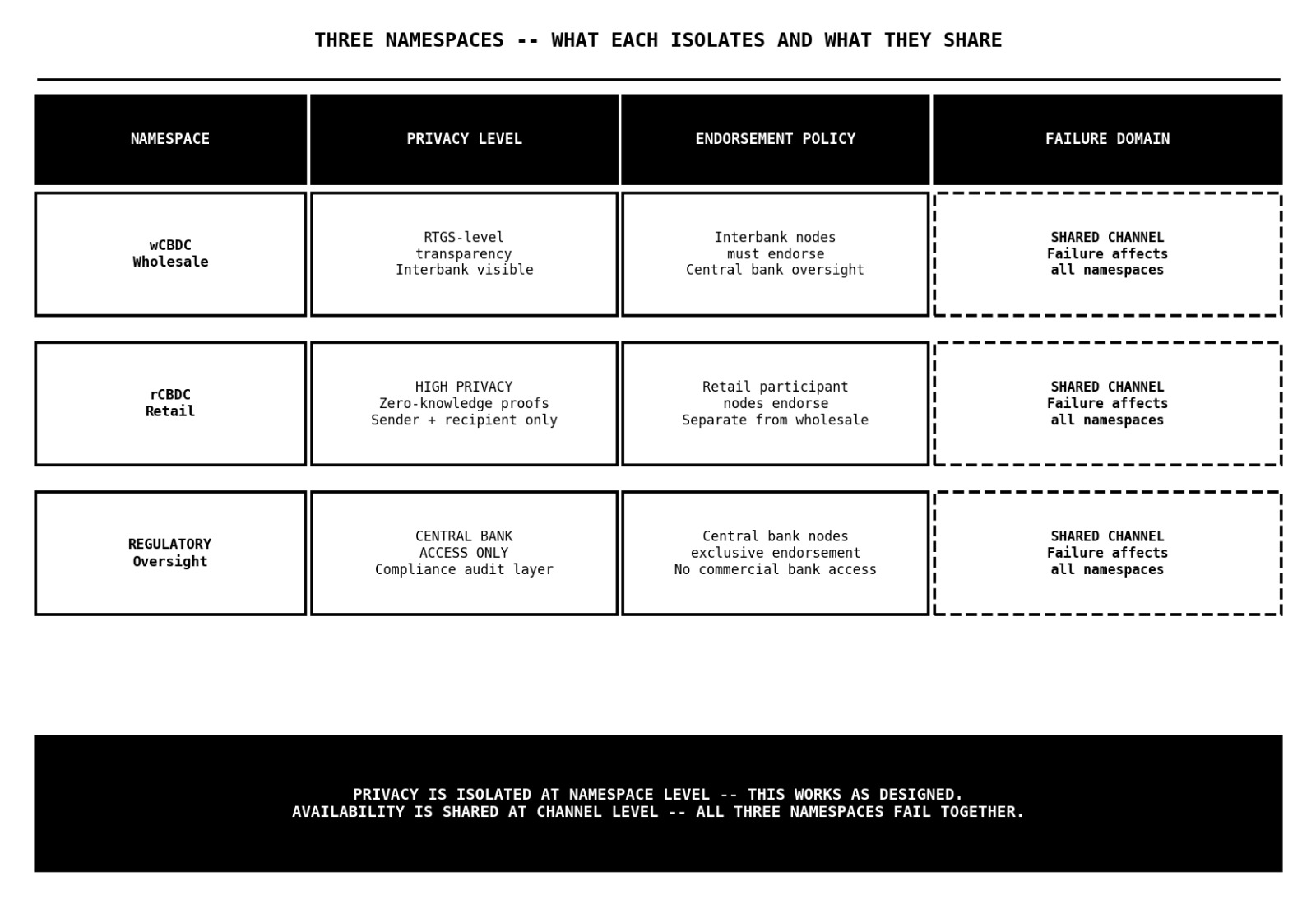
the SIGN design makes a different choice. one channel. three namespaces inside it. the wholesale CBDC namespace handles interbank settlements with RTGS-level transparency. the retail CBDC namespace handles citizen transactions with high privacy enforced through zero-knowledge proofs. the regulatory namespace gives the central bank oversight access with its own access controls.
each namespace has its own endorsement policy
that means the rules governing which nodes must validate and approve a transaction are defined independently per namespace. a retail CBDC transaction does not need to satisfy the same endorsement requirements as a wholesale interbank settlement. a regulatory query does not trigger the same validation path as a citizen payment.
the performance argument for this design is genuine
multi-channel Fabric architectures carry overhead. separate ledgers, separate ordering, separate membership management for each channel. by collapsing three channels into one with namespace partitioning, the architecture eliminates that overhead and lets the transaction dependency graph do its parallel validation work across a unified ledger.
What i think they got right:
the endorsement policy separation is genuinely well-designed. retail transactions carrying ZKP privacy protection and wholesale transactions operating with RTGS transparency have fundamentally different validation requirements. forcing them through identical endorsement logic would either over-constrain the wholesale layer or under-protect the retail layer.
keeping those policies distinct while sharing underlying infrastructure is the right instinct
the central bank gets unified oversight through the regulatory namespace without needing to reconcile separate ledgers. the privacy guarantees for retail transactions come from the ZKP layer, not from channel separation. and the operational complexity of running three separate channels with three separate orderer configurations is avoided entirely.
Where my concern sits:
the privacy model and the availability model are doing different jobs in this architecture and i dont think the documentation fully separates them.
namespace partitioning provides privacy isolation. a node participating in the retail namespace cannot read wholesale namespace transaction details. a participant without regulatory namespace access cannot inspect the central bank oversight records. that isolation is cryptographically enforced at the namespace level and it works.
but availability is a channel-level property. the channel is what connects nodes to the orderer, maintains the shared ledger, and coordinates transaction flow. if something goes wrong at the channel level - an orderer issue, a ledger inconsistency, a network partition affecting the channel itself - all three namespaces are affected simultaneously. the privacy boundaries between namespaces do not create availability boundaries between them.
in a traditional multi-channel deployment, a problem affecting the wholesale interbank settlement channel does not touch the retail citizen payment channel. the failure domain is bounded by the channel. in the single-channel design, the failure domain for all three namespaces is identical because they all share the same channel infrastructure underneath them
the whitepaper presents namespace partitioning as delivering the privacy benefits of channel separation without the operational overhead. that is accurate for privacy. it is not accurate for failure isolation. and for sovereign infrastructure where the retail CBDC serving millions of citizens shares a failure domain with the wholesale interbank settlement layer, that distinction is worth naming explicitly.
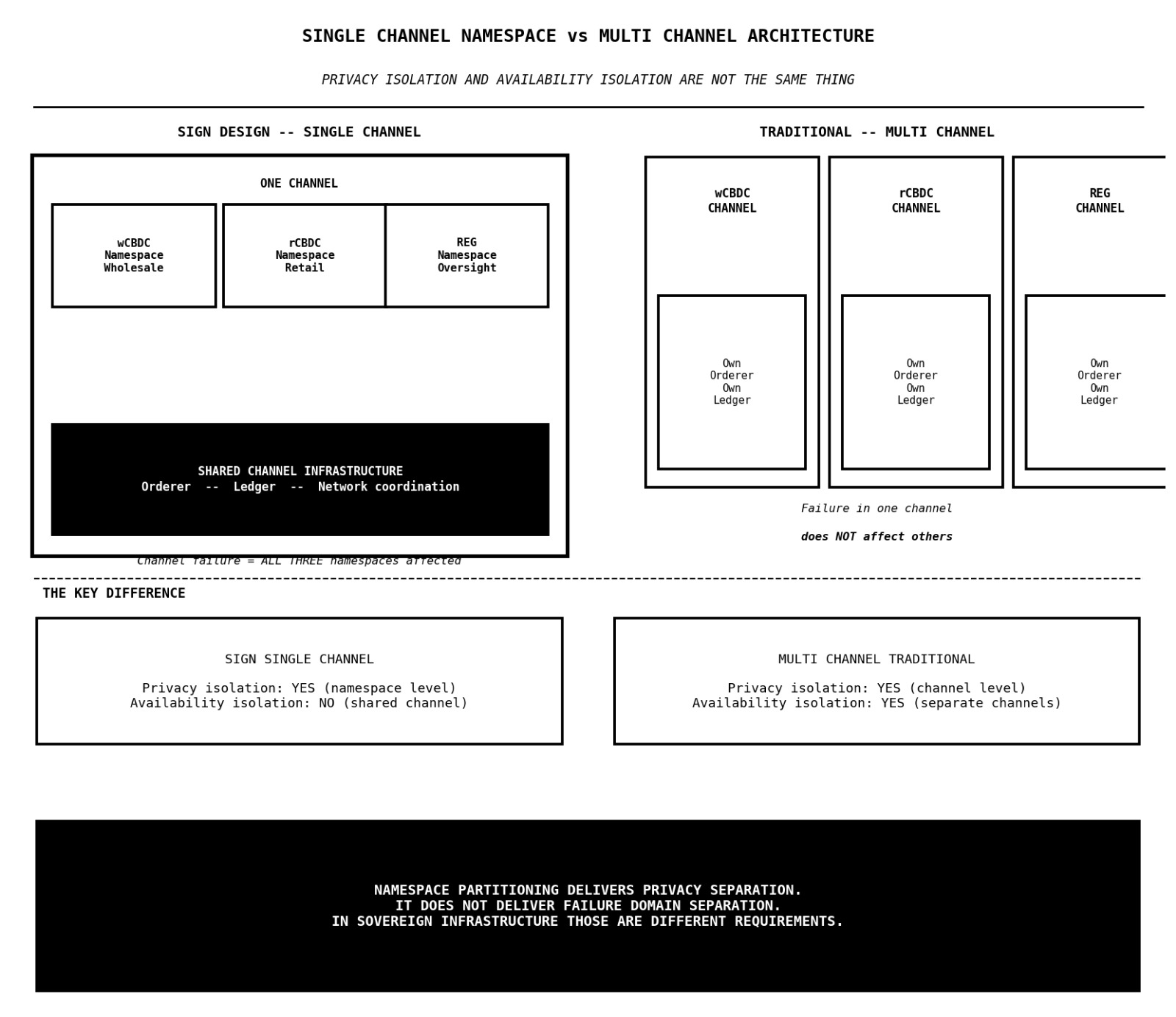
honestly dont know if the single-channel namespace architecture is a genuinely elegant solution that achieves privacy isolation without the cost of channel complexity or a design that quietly couples the availability of citizen payments to the stability of interbank infrastructure they were never meant to share?? 🤔
#SignDigitalSovereignInfra @SignOfficial $SIGN
