 I remember applying for a scholarship during university. The process required submitting detailed financial records: family income, personal savings, and even tax forms. At the time, I believed that handing over all this information was just part of the process, that institutions could be trusted to keep everything safe.But after hearing about data breaches and seeing peers’ documents misused or misplaced, I realized the system’s reliance on full disclosure created unnecessary risk. Sensitive financial information didn’t have to travel in the open; there had to be a way to prove eligibility without exposing private data. That experience reshaped how I evaluate privacy-focused projects today: I now focus on mechanisms that reduce operational risk while still enabling trust. Midnight Network stood out because it proposes exactly that kind of solution.That experience is why Midnight Network caught my attention. Not because it’s hyped or because zero-knowledge proofs are trendy. But because it raises a practical question: can students, or any participant, prove qualification criteria without revealing underlying sensitive data?For scholarships, grants, or financial aid, the core issue is verification friction. Institutions need certainty, while applicants want privacy. Midnight Network suggests a system where proofs are verifiable, auditable, and privacy-preserving. The real question becomes: does this approach actually reduce risk and friction in real-world administrative processes, or is it primarily theoretical?
I remember applying for a scholarship during university. The process required submitting detailed financial records: family income, personal savings, and even tax forms. At the time, I believed that handing over all this information was just part of the process, that institutions could be trusted to keep everything safe.But after hearing about data breaches and seeing peers’ documents misused or misplaced, I realized the system’s reliance on full disclosure created unnecessary risk. Sensitive financial information didn’t have to travel in the open; there had to be a way to prove eligibility without exposing private data. That experience reshaped how I evaluate privacy-focused projects today: I now focus on mechanisms that reduce operational risk while still enabling trust. Midnight Network stood out because it proposes exactly that kind of solution.That experience is why Midnight Network caught my attention. Not because it’s hyped or because zero-knowledge proofs are trendy. But because it raises a practical question: can students, or any participant, prove qualification criteria without revealing underlying sensitive data?For scholarships, grants, or financial aid, the core issue is verification friction. Institutions need certainty, while applicants want privacy. Midnight Network suggests a system where proofs are verifiable, auditable, and privacy-preserving. The real question becomes: does this approach actually reduce risk and friction in real-world administrative processes, or is it primarily theoretical?
 According to the documentation, Midnight Network works by issuing cryptographic proofs that validate a participant’s attributes without revealing the underlying data. Every applicant can generate proofs tied to their identity, which are then verified by institutions through the protocol.Think of it like a sealed envelope with a certified stamp: the recipient can confirm authenticity without opening it. In practice, a scholarship office can verify income brackets or other eligibility criteria without ever accessing the raw numbers.Validators in the network maintain uptime and accuracy, incentivized via protocol-native tokens. Misbehavior risks slashing, ensuring alignment with proper operation. This matters because traditional systems either require full exposure of sensitive data or rely on slow, manual verification. Midnight’s model reduces administrative friction while preserving privacy, potentially speeding approvals and reducing fraud.The market is already starting to take notice. As of March 2026, Midnight Network’s token trades around $0.38, with a circulating supply of roughly 85 million tokens and a daily trading volume near $950,000. Holder count sits around 12,400 addresses, indicating adoption is still early but measurable.These figures tell us that liquidity exists for operational activity, not just speculation. Moderate holder concentration suggests early institutional or developer engagement. Observing token distribution alongside proof generation metrics will reveal whether adoption scales beyond pilots, giving an early signal of the protocol’s real-world impact.
According to the documentation, Midnight Network works by issuing cryptographic proofs that validate a participant’s attributes without revealing the underlying data. Every applicant can generate proofs tied to their identity, which are then verified by institutions through the protocol.Think of it like a sealed envelope with a certified stamp: the recipient can confirm authenticity without opening it. In practice, a scholarship office can verify income brackets or other eligibility criteria without ever accessing the raw numbers.Validators in the network maintain uptime and accuracy, incentivized via protocol-native tokens. Misbehavior risks slashing, ensuring alignment with proper operation. This matters because traditional systems either require full exposure of sensitive data or rely on slow, manual verification. Midnight’s model reduces administrative friction while preserving privacy, potentially speeding approvals and reducing fraud.The market is already starting to take notice. As of March 2026, Midnight Network’s token trades around $0.38, with a circulating supply of roughly 85 million tokens and a daily trading volume near $950,000. Holder count sits around 12,400 addresses, indicating adoption is still early but measurable.These figures tell us that liquidity exists for operational activity, not just speculation. Moderate holder concentration suggests early institutional or developer engagement. Observing token distribution alongside proof generation metrics will reveal whether adoption scales beyond pilots, giving an early signal of the protocol’s real-world impact.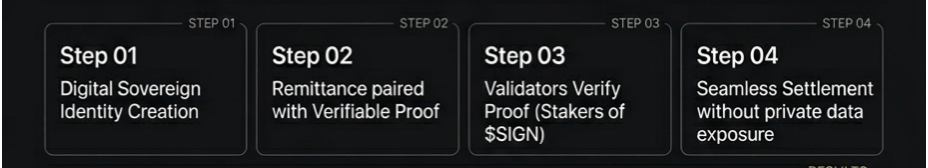
But this is where the real test appears. The biggest challenge isn’t price volatility or network design in theory. It’s actual usage and retention.If students, institutions, or validators do not consistently engage with the network, the cryptographic proofs remain an academic exercise. Validator performance, network uptime, and ease of integration with existing administrative systems will determine whether Midnight Network genuinely reduces friction.On the other hand, if adoption increases steadily, each participant strengthens network reliability. Conversely, poor integration, high friction, or regulatory obstacles could undermine early promise. The metric that really matters is whether proofs are actively used to replace traditional disclosure processes.So what would make me more confident? I’d want to see:
• Recurring use of proofs in real scholarship programs or financial aid applications.
• Validators maintaining high uptime without slashing events.
• Integration with multiple institutions demonstrating operational scalability.

I’d be more cautious if:
• Adoption remains limited to pilots with no repeat engagement.
• Validator performance is uneven, risking proof delays.
Tracking these indicators will clarify whether Midnight Network solves practical privacy problems or remains largely conceptual.
So if you’re following Midnight Network, don’t just watch price. Watch proof throughput and recurring usage. In systems handling sensitive financial or personal data, the difference between hype and functional impact is simple: a protocol either reduces exposure risk while maintaining trust, or it doesn’t.The real insight: privacy isn’t just about encryption—it’s about designing systems that let people prove what they need without revealing what they shouldn’t. That’s where lasting value emerges.
#night || @MidnightNetwork || $NIGHT

