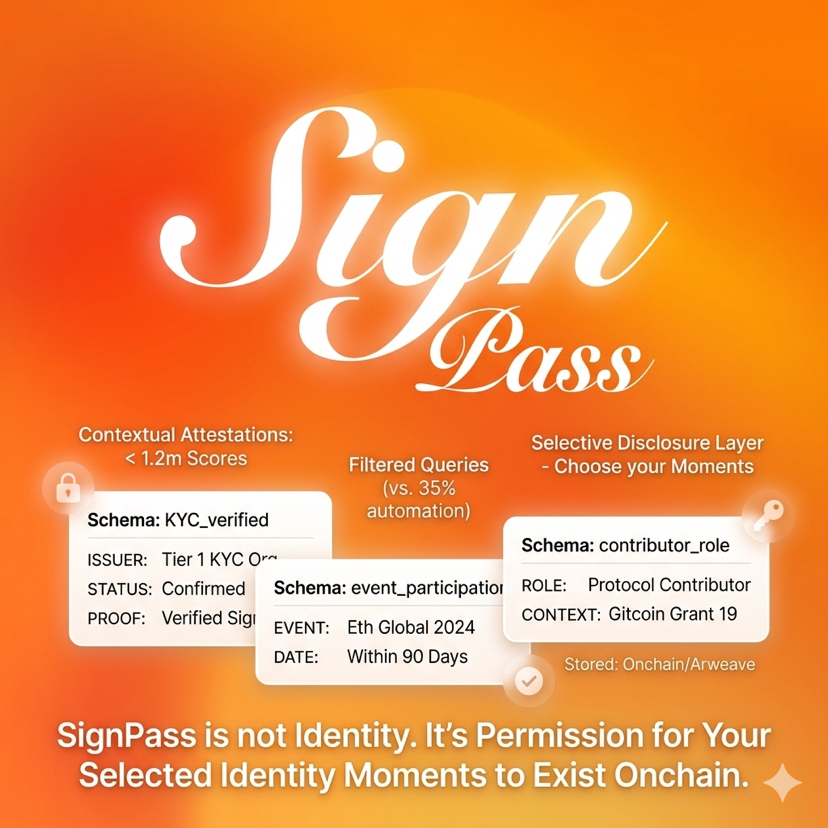
The SignPass of @SignOfficial is not identity. It's how you choose which moments of your life are allowed to exist on-chain. I realized this not while reading the documentation, but while looking back at a very specific case.
In March 2024, a Sybil farming operation on Gitcoin Passport was exposed. Over 1.2 million “identity scores” were generated, but internal analysis showed that over 35% of accounts exhibited signs of automation. The system wasn't faulty; it was trying to gauge your identity by gathering all possible signals.
That's the problem. The more you group things together, the more likely it is to cause confusion. One line in the Sign Protocol documentation is particularly noteworthy: "Attestations are contextual, not universal identity claims." It's not the definition itself, but the way they choose to take a side.
If you read carefully, SignPass is just a class to query and display those attestations based on context, not a profile, not a DID, and not an overall reputation score.
Each attestation in @SignOfficial is associated with a schema. The schema defines the data structure, for example: KYC_verified, event_participation, contributor_role. The attestation is signed by the issuer, and storage can be on-chain or off-chain via Arweave or optional storage.
The key difference isn't where it's stored. SignPass uses an indexing layer to map addresses to schema-based attestations. SignPass essentially queries this layer and then filters based on the dApp's conditions. It doesn't fetch everything and display it, but rather resolves only the necessary schema.
Here's a specific example. A dApp requires that "the user has completed KYC at issuer X and has participated in event Y in the last 90 days." SignPass doesn't need to reveal the entire history; it only needs to return two attestations that meet the criteria, along with proof of signatures. The rest doesn't exist within the dApp.
Unlike Worldcoin, where they anchor identity to iris hash and global uniqueness, SignPass completely rejects the question: who are you?
Unlike Polygon ID, where zero knowledge proof is used to demonstrate attributes, SignPass doesn't attempt to conceal anything mathematically. It chooses not to expose anything from the outset.
Cryptography is less complex. It's more dependent on system design. Another data point worth considering.
According to data from Chainalysis, approximately 60% of necromancy in crypto doesn't come from hacks or leaks, but from correlations between transaction patterns and external datasets. This means you don't need to reveal information.
The system still infers. SignPass cuts right here. If the data doesn't exist, there's nothing to correlate. It sounds obvious. But very few systems dare to do it thoroughly. The risk isn't in privacy. It's in trust. The issuer becomes the bottleneck.
An attestation from a tier 1 KYC organization and an attestation from a Discord bot can share the same schema. If the dApp doesn't filter the issuer, SignPass will return both as the same. There is no ground truth. Only who signed.
If each project defines its own schema for "verified users," the ecosystem will break into many small pieces. SignPass would then only be a tool for reading fragmented data.
It's like Web2 in its early days with its badge system. There were badges, but nobody agreed which badges were meaningful.
This is a particularly sensitive time. As Ethereum pushes for account abstraction, wallets are no longer fixed identities. Session keys and smart accounts are making identities more fluid.
SignPass fits right into that space. It doesn't lock you up. It only records what has been confirmed.
Or to put it more simply: Traditional identity tries to answer "who you are." SignPass answers "who has verified you, and under what circumstances," completely eliminating the need to build a complete profile.
It will fail if there aren't enough trustworthy issuers, if the schema doesn't converge, or if the dApp is too lazy to filter. It works when trust is clearly tiered and context is respected. Not identity. It's permission for a part of the identity to appear.
Perhaps we will soon have to relearn how to question identity in the digital environment — no longer "is it built enough?", but "is it too much already revealed?". SignPass doesn't offer a common standard for all systems to agree upon, but opens the possibility for each context to define its own level of "trustworthiness".
This can cause the ecosystem to become more fragmented before it has a chance to converge.
But it is precisely this fragmentation that allows new trust models to be tested, rather than being rigidly standardized too early.
And perhaps, the real value lies not in defining who you are, but in the right not to have to answer that question, unless you choose.
$SIGN #SignDigitalSovereignInfra
