 I remember a time when I followed a wave of privacy-focused tokens during a market cycle where “data protection” was the dominant narrative. At the time, I believed that any project mentioning encryption or anonymity had long-term value. The assumption felt logical because privacy is something everyone talks about but few truly understand.But after looking deeper, I realized that most of these systems were not solving real-world friction. They were either too complex for institutions to adopt or too isolated to integrate into existing systems. The technology existed, but the usage did not follow.That experience changed how I evaluate privacy projects today. I stopped focusing on what they promise and started asking a simpler question. Where does this actually reduce friction in real life?That experience is why Midnight Network caught my attention.Not because it promotes privacy as a broad concept, but because it focuses on controlled disclosure rather than full secrecy.It raises a practical question.What if a patient could prove eligibility for treatment or insurance without exposing their entire medical history?
I remember a time when I followed a wave of privacy-focused tokens during a market cycle where “data protection” was the dominant narrative. At the time, I believed that any project mentioning encryption or anonymity had long-term value. The assumption felt logical because privacy is something everyone talks about but few truly understand.But after looking deeper, I realized that most of these systems were not solving real-world friction. They were either too complex for institutions to adopt or too isolated to integrate into existing systems. The technology existed, but the usage did not follow.That experience changed how I evaluate privacy projects today. I stopped focusing on what they promise and started asking a simpler question. Where does this actually reduce friction in real life?That experience is why Midnight Network caught my attention.Not because it promotes privacy as a broad concept, but because it focuses on controlled disclosure rather than full secrecy.It raises a practical question.What if a patient could prove eligibility for treatment or insurance without exposing their entire medical history?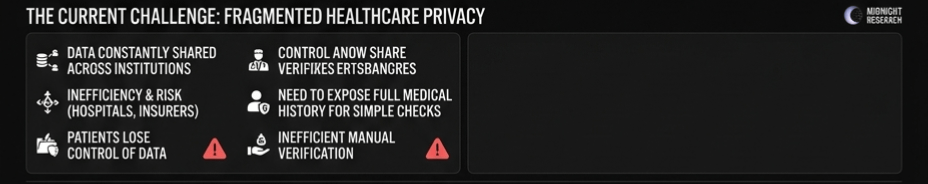
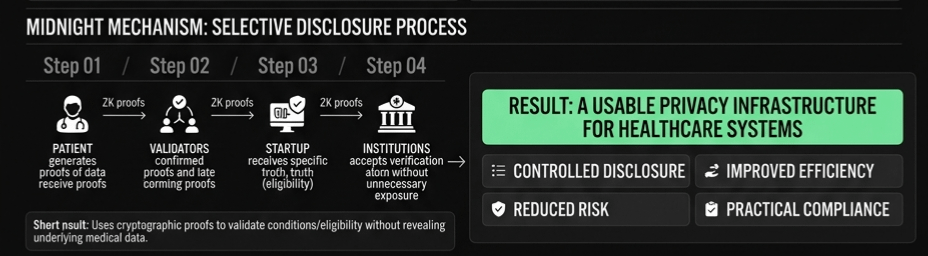
In healthcare systems, data is constantly shared across hospitals, insurers, and third parties. This creates both inefficiency and risk. Patients often lose control over their own information.So the real question becomes.Can a network like Midnight allow verification without unnecessary exposure, and does that actually improve how healthcare systems function?According to the project documentation, Midnight Network is designed around privacy-preserving smart contracts and selective data disclosure. Instead of broadcasting all transaction or data details publicly, it uses cryptographic techniques to validate information while keeping the underlying data hidden.The protocol works by allowing users to generate proofs about their data. For example, a patient does not need to share full medical records. Instead, they can prove a specific condition, eligibility status, or compliance requirement without revealing unrelated details. simple way to understand this is to compare it with showing identity at a checkpoint. Normally, you hand over your entire ID card. $A2Z and $JCT both highlight how verified identity and trust signals can feed into Midnight’s selective disclosure model, where data is not shared openly but proven only when required.With Midnight, you only prove the one thing required, such as age eligibility, without revealing your name or address.This approach relies on advanced cryptographic methods where validators confirm the truth of a statement without accessing raw data. The network ensures that these proofs remain verifiable while maintaining privacy at the base layer.The token plays a role in securing the network and supporting computation. Validators participate in processing these privacy-preserving operations, and incentives are aligned to maintain reliability and correctness.This matters in healthcare because trust is not just about accuracy. It is about control. Patients want systems that allow them to share only what is necessary, especially in regions where digital health infrastructure is still evolving.
The market is gradually paying attention to this category of privacy infrastructure.Midnight Network, while still developing its broader ecosystem presence, has started to attract interest from communities focused on data protection and compliance-based systems. Token activity reflects early-stage participation rather than mature adoption, which is typical for infrastructure projects at this stage.Trading activity shows moderate but consistent engagement, suggesting that the project is being observed rather than heavily speculated on. Holder distribution appears to be expanding slowly, which often indicates organic discovery rather than rapid hype-driven inflows.From a broader perspective, privacy narratives tend to move in cycles. However, what is different here is the shift toward practical applications such as healthcare, finance, and identity systems. These sectors require more than theoretical privacy. They require usable frameworks.These early signals suggest that the market sees potential, but it has not yet fully priced in real-world adoption.But this is where the real test appears.The biggest challenge for Midnight Network is not whether the technology works. Privacy-preserving computation has been researched for years. The challenge is whether institutions will actually integrate it into their workflows.The key metric here is real usage in regulated environments.Healthcare systems are complex. They involve legal compliance, legacy infrastructure, and multiple stakeholders. Even if a privacy solution is technically superior, adoption depends on how easily it fits into existing processes.If hospitals and insurers do not use these selective disclosure proofs regularly, the system does not create meaningful impact. 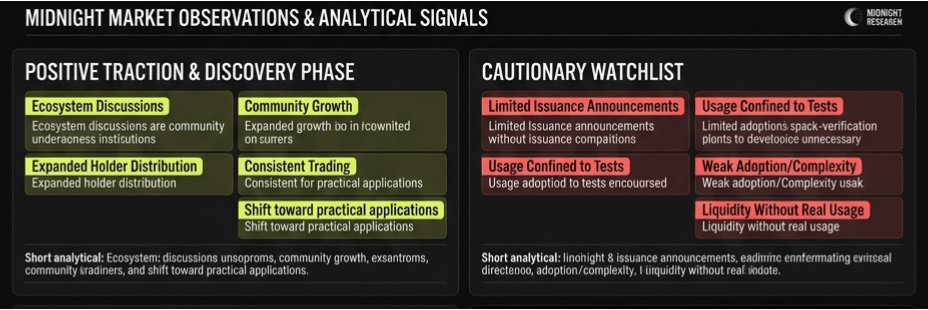
It remains a tool without a workflow.On the other hand, if patients and institutions begin to rely on these proofs for everyday verification, the network gains strength. Each new interaction reinforces trust and reduces reliance on traditional data-sharing methods.This creates a clear dividing line.Without repeated usage, privacy remains a feature.With consistent usage, it becomes infrastructure.So what would make me more confident in Midnight Network?I would want to see real partnerships with healthcare providers where selective disclosure is used in actual patient interactions. Not just pilot announcements, but continuous usage tied to real cases.Another important signal would be integration with insurance systems. If eligibility checks start relying on privacy proofs rather than full document sharing, it would indicate practical value.I would also watch developer activity closely. Applications built on top of the network often reveal whether a system is becoming usable or remains theoretical.At the same time, I would be cautious if adoption stays limited to test environments or isolated demonstrations. If institutions hesitate to integrate due to complexity or regulatory concerns, growth could slow significantly.Liquidity without usage would also be a concern. It often signals that the narrative is ahead of actual implementation.Midnight Network, it is worth shifting focus away from short-term attention.Watch how often these privacy proofs are actually used in real systems.In healthcare, trust is not built through promises. It is built through repeated, reliable interactions where sensitive data is handled carefully.The difference between an idea and real infrastructure is not complexity. It is consistency.In markets like this, many projects can demonstrate privacy. Very few can make it part of everyday decisions.And in the long run, the systems that survive are usually the ones people keep using when privacy stops being optional and starts becoming necessary.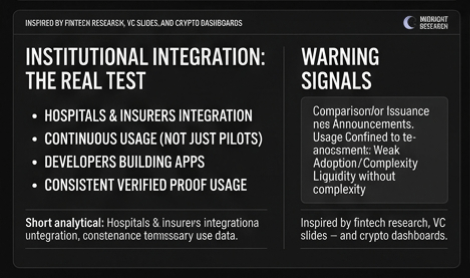
#night $NIGHT @MidnightNetwork

