@MidnightNetwork Using a 'living city' to drag rational privacy from white papers into a breathing reality.
AI agents: 'living' residents built on psychological theory
In this #night city, each AI agent is powered by Google Gemini, possessing long-term memory context and completely independent personality, goals, and motivations. The official six-dimensional personality model is clearly based on personality psychology theory—multi-dimensional psychological portraits, allowing agents to 'grow' like real people: they can autonomously initiate transactions, socialize, and start businesses, yet never expose their intentions. Only zero-knowledge proof results are visible on-chain, while the underlying personality, history, and decisions are all securely stored locally.
Jung's archetypal theory was originally a map of the human mind, but now it has been appropriated by Midnight to 'create a soul' for AI agents. The AI agents are not scripts, but psychological individuals that can be 'hurt' and 'evolve', perfectly interpreting rational privacy: proving who you are without allowing you to be defined. I instantly felt a sense of familiarity like an old friend, where personality is no longer an abstract theory but an individual that can 'live' on the chain. Next, I will discuss the shortcomings of night.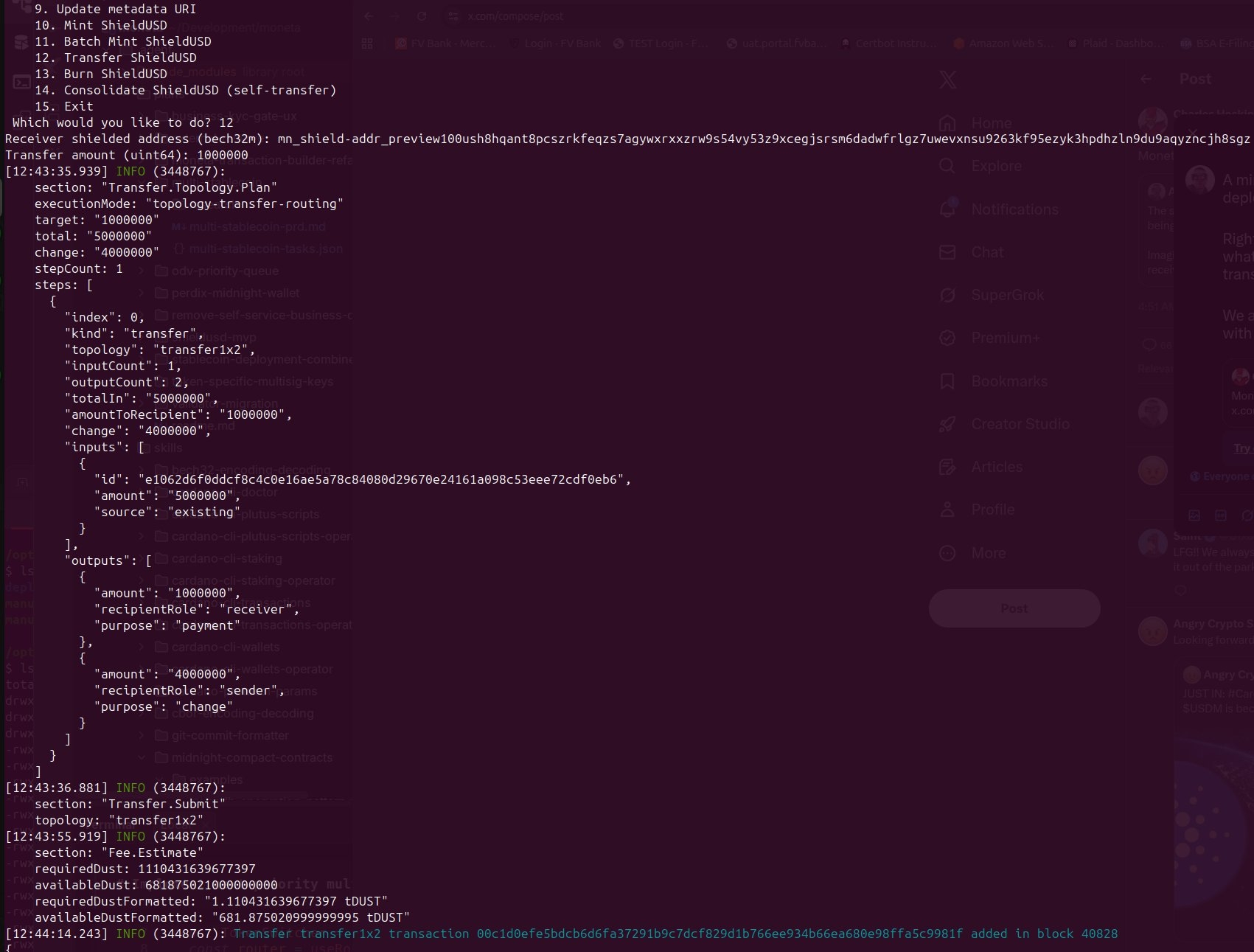
I just got the@MidnightNetwork set of Kachina framework running in the test environment, and it felt like I had personally dismantled a rusty precision instrument. The current Web3 is indeed a tale of the emperor's new clothes, loudly proclaiming sovereignty while the body runs naked under the spotlight of public chains, all transaction flows appear more pale than blank paper in front of analytical tools. Midnight's thrown out$NIGHT , essentially installs one-way reflective glass on this transparent prison, using zero-knowledge proofs to allow users to decide who to show their data to. Opening its codebase, you can feel the nearly obsessive balance of the IOG geeks: they don’t want to be the kind of assassin that disappears into darkness like Monero; they want to be the suited hackers trying to walk the tightrope between privacy and compliance audits. As I chew on the already cold pizza, watching the console continuously refresh the Proof verification, this ambition is indeed charming: reconstructing trust models on sidechains, presenting precision privacy scalpels to those greasy Web2 developers with Typescript. This suited hacker narrative is extremely elegant, but when I actually try to perform surgery, the blade hits a few hard hidden reefs.#Night 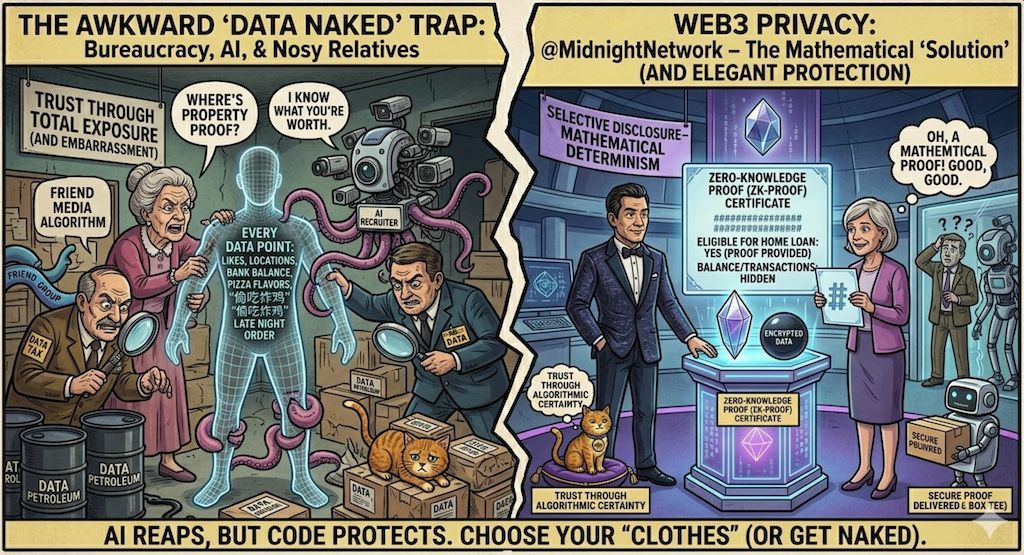
But here I noticed several pain points that are not easy to detect; the most intuitive pain point is the computational load caused by private state management. Even with ZK algorithms, the computational power demand for clients to generate proofs may still overwhelm lightweight devices, making this surgical knife feel incredibly heavy at the fingertips. The deeper hidden dangers lie in the game between compliance and privacy: that finely crafted selective disclosure mechanism can easily become a form of a backdoor under audit pressure, rendering decentralized censorship resistance illusory under the regulatory lighthouse. Meanwhile, the discontinuity of off-chain data availability runs counter to the developers' accustomed O(1) read-write logic, and blind operation debugging in an encrypted state is a nightmare for engineering implementation. If a true balance cannot be found between proof performance and the decentralization of power distribution, the one-way reflective glass meticulously crafted by Midnight will likely end up being just a digital showroom with surveillance cameras.
