I remember a period when I was too focused on the stories surrounding identity protocols. At that time, anything related to digital identity felt like the next obvious cycle. I assumed that if a project talked about ownership and verification, it automatically meant long-term value. But after looking deeper, I realized that most systems are incomplete. They issue identities, but do not make them usable in real economic activity. There is no bridge between ownership and application. That experience changed the way I evaluate projects today. I no longer look at what a system promises on the surface. I look at whether identity actually flows into transactions, agreements, and usage in the real world. That shift in thinking is why Sign captured my attention. Not because it talks about sovereignty or control, as many projects have done that. But because it poses a more practical question. What happens after an identity is created? How does it move within an economy? So, the real question becomes whether this system can turn identity into infrastructure that businesses, governments, and individuals can actually use. Especially in areas like the Middle East, where trust, compliance, and cross-border coordination are very important, this question becomes not just technical. It becomes economic. According to project documentation, the Sign Protocol is designed as a layer of trust where identities, agreements, and certificates are verified on-chain in a structured manner. Instead of viewing identity as a static record, the system sees it as something dynamic that interacts with applications. The protocol works by allowing entities to issue certifications. These certifications act as verified statements. They can represent anything from ownership to qualifications or contractual agreements. Each certification is cryptographically signed and stored in a way that can be referenced by other applications. A simple way to think about this is as a digital notary system combined with an application layer. Imagine a business issuing a certificate to a supplier. Instead of storing that record privately, it becomes a verifiable object on-chain that other systems can trust. Developers can build applications that read and utilize these certifications. This creates a network effect. The more certifications that exist, the more useful the system becomes. Tokens play a role in coordinating this operation. They support governance and adjust incentives for those participating in maintaining and validating the system. This is important because without proper incentives, verification layers are often not fully utilized. In markets where trust is fragmented, such a system attempts to standardize how verification is created and consumed. The market has already shown some degree of attention. As of now, $MAGMA demonstrates how liquidity can be effectively coordinated, but Sign adds a layer of trust that makes identities and agreements verifiable for real economic use. According to recent observations, trading tokens in a range reflects an early-stage position rather than full maturity. The market capitalization remains modest compared to more established infrastructure projects, suggesting that expectations are still forming. Daily trading volumes show local spikes, often related to announcements or integrations rather than stable organic demand. The distribution of holders appears to be expanding, although still concentrated enough to suggest that long-term participation is not yet fully decentralized. These numbers suggest that the market is valuing potential rather than proven adoption. There is interest, but it remains unclear whether that interest is driven by actual usage or by positioning ahead of anticipated growth. This distinction becomes important when assessing sustainability. But this is where the real test emerges. The biggest challenge is not whether the protocol can issue certifications or support identity verification. It is whether these certifications are actually used repeatedly in real economic flows. Maintenance and usage become defining variables. If developers build applications that rely on these certifications, the system will become stronger over time. Each new use case reinforces the network. But if certifications are created without being referenced or reused, the system risks becoming a static database rather than a dynamic infrastructure layer. In that scenario, the demand for tokens becomes dependent on speculation rather than utility. For the Middle East, this risk becomes even more relevant. The region has strong potential for digital infrastructure development, but adoption depends on integration with real-world organizations. Governments, businesses, and financial systems must find value in using such a protocol. If that integration does not happen, the system retains its technical nature but is constrained economically. So the key question is not whether identity can be verified. But whether that verification becomes a part of everyday operations. $RDNT demonstrates how capital flows through markets, while Sign ensures that those flows are supported by verifiable identities and trustworthy interactions. Who is consistently issuing certifications? Who is consuming them? And what incentives keep them engaged over time? So what would make me more confident in this system? I want to see consistent growth in the use of certifications across multiple applications, not just isolated cases. I will also look for partners connecting the protocol with real economic entities such as financial institutions or regulatory bodies. Another important signal will be developer activity. If builders are creating applications that rely on these certifications, that indicates the system is becoming embedded in workflows. Conversely, I would become more cautious if usage remains event-driven rather than continuous. Spikes followed by inactivity would suggest that adoption is unstable. I would also monitor the risk of over-reliance on incentives. If participation declines as rewards decrease, that indicates weak organic demand. So if you are tracking this project, don’t just focus on price volatility. Pay attention to the frequency with which identities are actually used in applications. In such markets, the difference between perceived value and real infrastructure is often very simple. The critical systems are not those that create identity. They are those that identity continues to flow through even when no one is paying attention.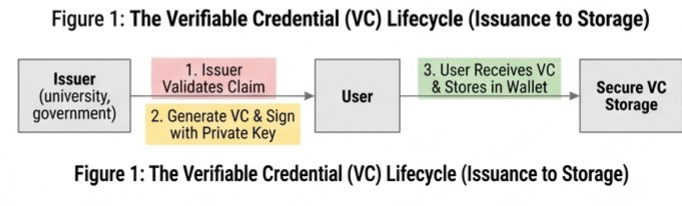
Article
From Identity to Infrastructure: Assessing the Role of Sign in Middle Eastern Economic Systems
Disclaimer: Includes third-party opinions. No financial advice. May include sponsored content. See T&Cs.
0
0
454
Explore the latest crypto news
⚡️ Be a part of the latests discussions in crypto
💬 Interact with your favorite creators
👍 Enjoy content that interests you
Email / Phone number