After delving into Midnight's anti-spam architecture, I was amazed by its ZK proof asymmetrical cost mechanism. This is an exceptionally clever security design within the protocol, yet it is rarely discussed in depth.
People generally focus on DUST fee control and network congestion, while overlooking the cost asymmetry advantages brought by underlying cryptography. Protected transactions must generate ZK proofs to demonstrate the legitimacy of DUST; generating these proofs incurs extremely high computational costs, while network verification is incredibly low-cost. This mathematical property inherently creates a security barrier.
In traditional public chains, attackers face the same transaction costs as regular users, relying solely on fees to prevent attacks. However, on Midnight, attackers must bear the massive cost of proof generation when sending large batches, while the burden of network verification is very light, resulting in a disparity in attack and defense costs. Coupled with a dynamic fee mechanism, network congestion increases DUST costs, and failed attacks require regenerating proofs, causing attack costs to continuously accumulate with no profit.
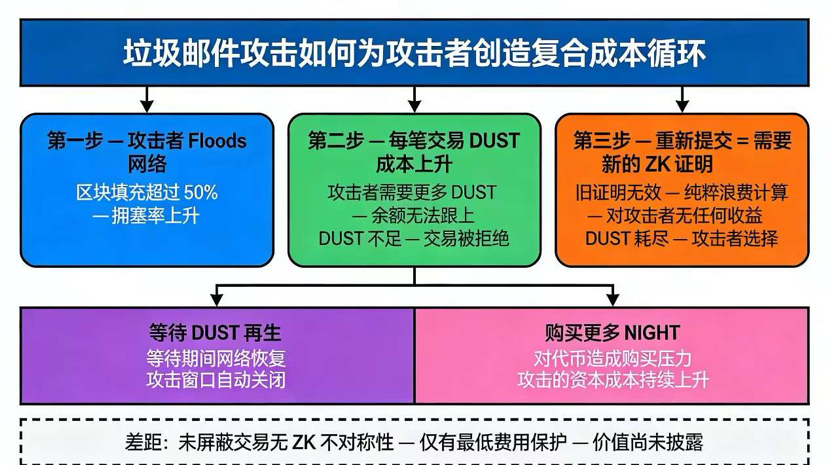
At the same time, the DUST output is limited by NIGHT's holdings, malicious attackers have limited resources, and after exhaustion, they need to wait for recovery or increase their holdings, further raising the threshold for attacks, while rational attackers will actively give up.
However, this design has obvious shortcomings: the network supports unprotected transactions, requiring no ZK proofs or DUST, relying solely on minimal fees for defense. If the fee parameter is set too low, this dimension can easily become a breakthrough point for attacks, lacking ZK asymmetric protection.
Overall, Midnight combines cryptography and token economics to create a layered defense system, with top-notch protection for protected transactions. However, the security of unprotected transactions relies on governance parameter settings, which poses certain risks.
Do you think this is a top-notch anti-spam design in privacy chains, or a semi-finished product with obvious protection gaps @MidnightNetwork