Once she talked to me about a case: a patient wanted to sue the hospital and needed to prove that the diagnostic records had not been tampered with. But the hospital system is centralized; whoever manages the records can modify them. The 'original record' she obtained had almost no evidential power in court. She said: the truth does not not exist; rather, the truth has no carrier.
I didn't think too much at the time until I later came across @MidnightNetwork and realized that this is not an isolated case; it is a structural gap in the credibility of data in the entire digital age. Data exists, but authenticity is lost; records exist, but evidential power is lost.
Midnight uses ZK Snarks, and its core is one thing: to allow the prover to convince the verifier that something is true without revealing any additional information.
How is it specifically implemented? Several key steps:
The first step is arithmetic circuit construction. The statement to be proven is translated into a mathematical circuit, with all computational constraints encoded. This step determines what you can and cannot prove.
The second step is witness generation. The prover has a secret input that satisfies all constraints of the circuit, but cannot directly tell the verifier.
The third step is proof generation, utilizing elliptic curve pairing and homomorphic commitments—complex mathematical operations that result in a compact proof, whose size does not grow linearly with the complexity of the statement being proven (this is the source of 'conciseness').
The fourth step is for the verifier to obtain the proof, public parameters, and the original statement, run the verification algorithm, and confirm the proof's validity—this whole process does not require the prover to be present and does not require back-and-forth communication (this is the source of 'non-interactive').
What does this mean for my friend's medical record issue? It means that a patient can prove "the state of my record at a certain point in time is X" without needing to disclose the entire medical record to the court—selective disclosure, only proving the part that needs to be proven.

Midnight has a technology called Kachina, which is used to solve the privacy problem of smart contracts. Many people think that a privacy blockchain is just "encrypting the transfer amount," but this understanding is far off.
The real challenge is: smart contracts involve not just numerical values, but stateful computational logic. During the execution of a contract, there are inputs, intermediate states, and branching decisions, and once these things are on-chain, they all become public information.
Midnight's Kachina protocol is specifically designed to solve this problem.
The core model of Kachina is a dual-state machine:
Public state: exists on-chain, visible to all nodes, used for achieving consensus.
Private state: exists on the user's local machine, readable only by the key holder.
How do these two states interact? Through ZK proofs as a bridge. When a user wants to execute a contract action, they need to prove under zero knowledge: "A change in my private state reasonably leads to this update in the public state"—the node verifies the validity of this assertion, not the private state itself.
Kachina is based on the UC (Universal Composability) security framework, one of the strictest frameworks for protocol security in cryptography—it requires that the protocol maintains its security in any environment and when combined with other protocols. In other words, Kachina's security guarantees are not 'under ideal conditions,' but 'in real, complex systems.'
There’s also a design detail that is easily overlooked: Kachina achieves concurrency control through a transcript mechanism. When multiple users interact with the same contract simultaneously, the system uses interaction records to order and verify operations, maximizing throughput while minimizing information leakage. This is an engineering problem that many privacy chains have not solved well—sacrificing performance for privacy, while Kachina attempts to achieve both.
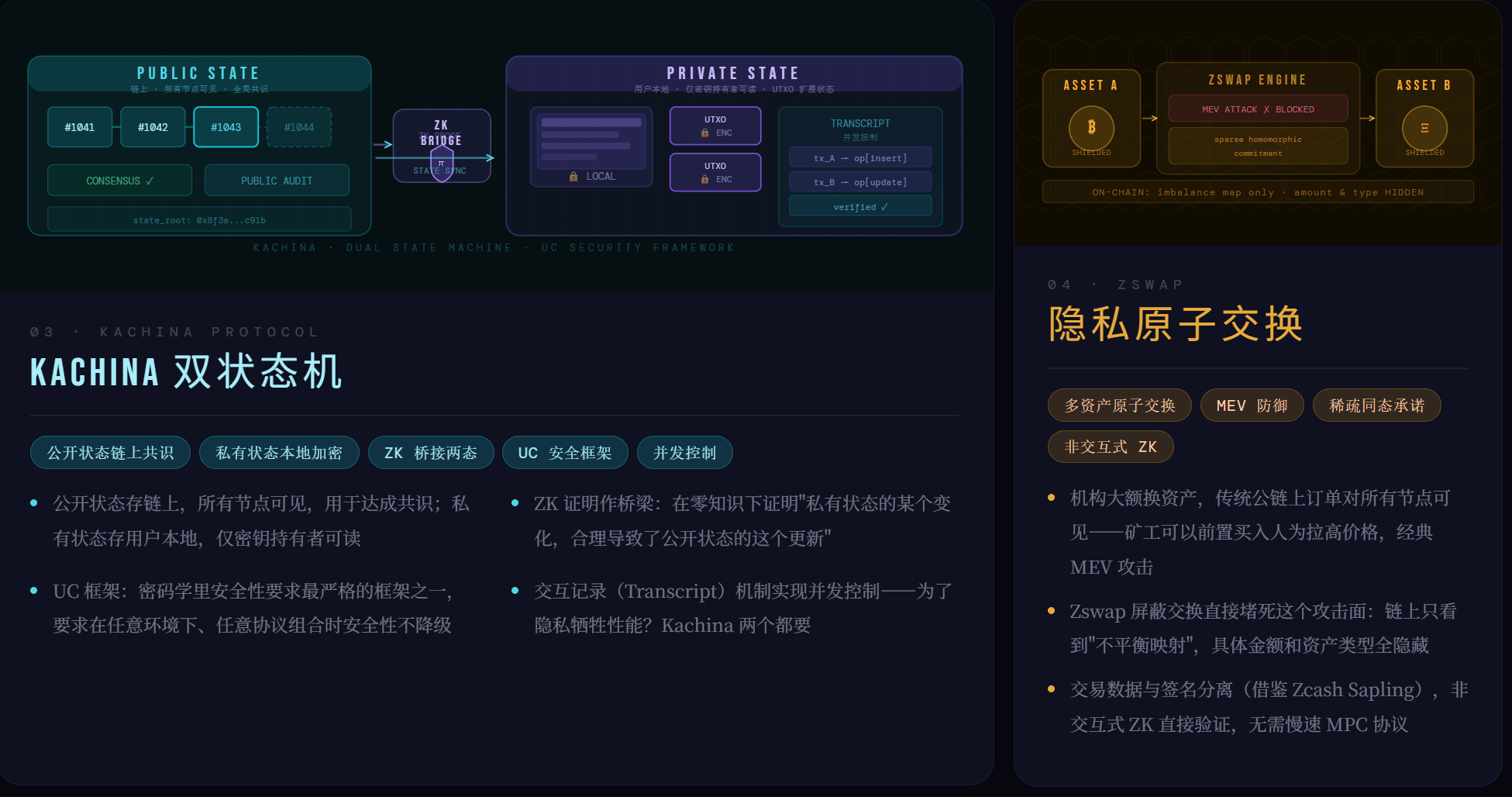
After explaining the underlying proof system, let me tell you where Midnight's Zswap is used.
Zswap is Midnight's multi-asset privacy atomic swap protocol, evolved from the Zerocash protocol, with a core of sparse homomorphic commitments + non-interactive zero-knowledge proofs.
Atomic swap itself is not a new concept; it addresses the issue of trustless asset exchange. Zswap adds a layer on top of that: making the details of the swap itself invisible to on-chain observers.
Why is this important? To give a direct example: if an institution wants to swap a large asset on-chain, this order is visible to all miners and nodes on a traditional public chain. Miners can buy in advance before the order executes, artificially raising the price and then selling it to you, which is a classic MEV attack. Zswap's shielded swap directly blocks this attack vector.
In terms of technical implementation, Zswap separates transaction data and signatures, a design concept borrowed from Zcash Sapling. After separation, non-interactive zero-knowledge proofs can directly verify transaction data without requiring slow multi-party computation (MPC) protocols. The design of sparse commitments makes merging multiple transactions possible, and on-chain, only the 'imbalance map' of each asset—the difference between inputs and outputs—is visible, with specific amounts and asset types completely hidden.
For DeFi, this opens a truly meaningful door: institutional-level on-chain liquidity management, without worrying about being front-run.
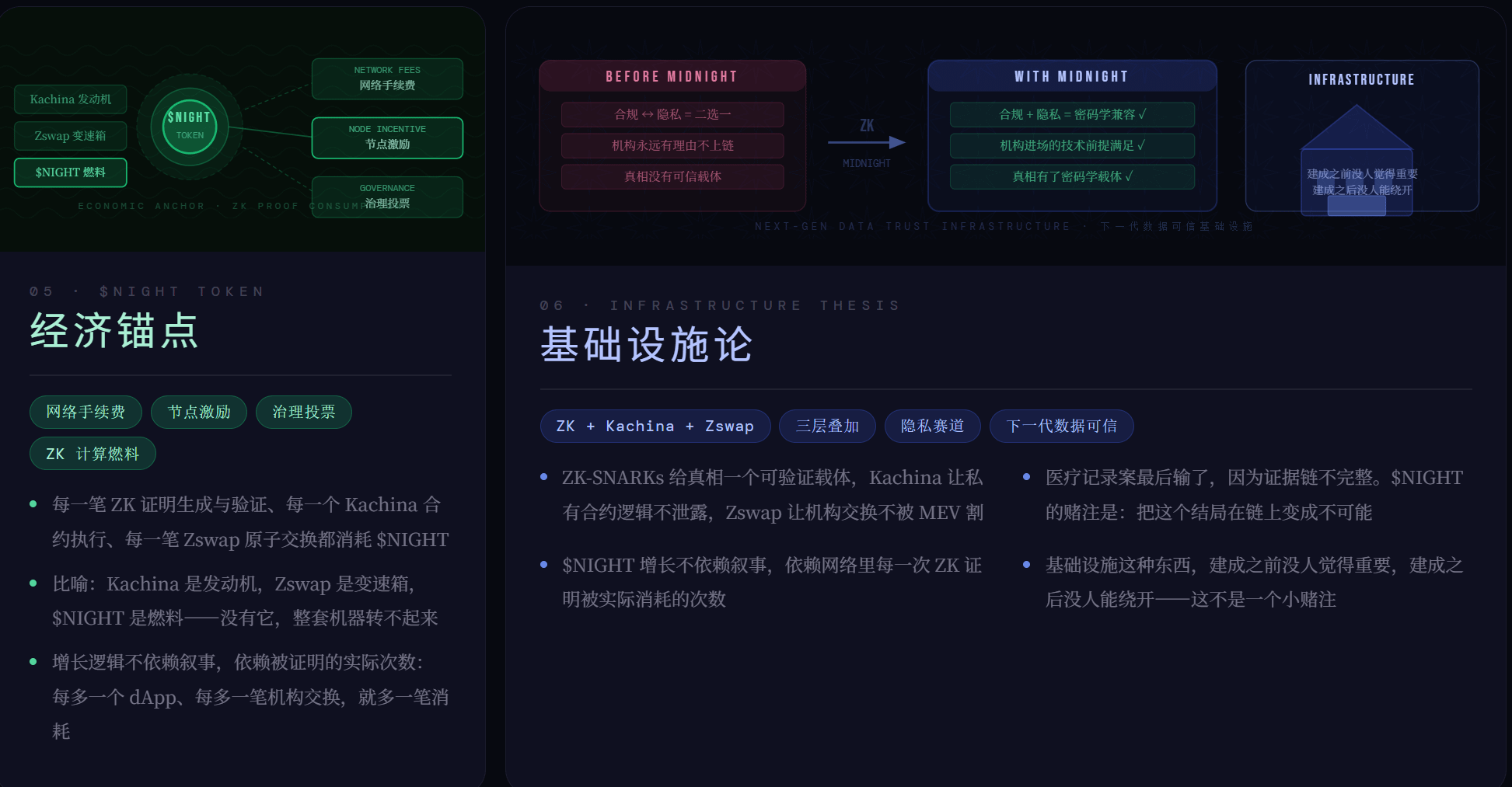
After discussing so much technology, some friends must be wondering: what is the function of $NIGHT ?
$NIGHT is the native token of the Midnight network, serving three core functions: network fees, node incentives, and governance voting. More importantly, it is irreplaceable in the entire privacy infrastructure, as every ZK proof generation and verification, every execution of a Kachina contract, and every atomic swap of Zswap requires the economic anchor of consuming NIGHT computational resources.
To put it metaphorically: Kachina is the engine, Zswap is the transmission; without NIGHT, the entire machine cannot operate.
The growth logic of NIGHT's network value does not rely on narratives but on the actual number of proven instances. For every additional dApp using Kachina to handle private contracts, and for every institutional use of Zswap for shielded swaps, there will be an additional renewal of NIGHT's usage.
Returning to the medical record case I mentioned at the beginning, they lost in the end due to an incomplete chain of evidence.
She said a sentence that I remember to this day: "It’s not that the truth does not exist, it’s that the truth has no carrier."
This statement holds true on-chain as well. The data is available, but the trusted carrier is not; privacy is desired, but verifiability is lost. Before Midnight, the entire industry survived by circumventing this contradiction.
@MidnightNetwork 's bet is: ZK Snarks + Kachina + Zswap, three layers stacked, providing a carrier for data truth that satisfies both privacy and trust. This is not a small bet. But if it pays off, the concept of Midnight in this private lane is the economic core of the next generation of trusted data infrastructure.
Infrastructure is something that no one thinks is important before it is built, and no one can bypass once it's built.
