In the many years of evolution of blockchain technology, privacy protection has always been the last barrier between 'decentralization' and 'mainstream adoption.' With the official launch of the 2026 March @MidnightNetwork network mainnet, the privacy token track is undergoing a profound transformation from 'absolute anonymity' to 'programmable, compliant privacy.' This article will take the core architecture of Midnight as a starting point to analyze the medium and long-term trends in the privacy track from a data-driven perspective.#night

1. Deep Deconstruction of Midnight ($NIGHT) Architecture: Reshaping Privacy Foundations
Midnight is not a traditional privacy coin (like Monero); it is a fourth-generation privacy computing layer built using zero-knowledge proofs (ZK). Its architecture design precisely addresses the long-standing conflict between privacy protection and regulatory compliance.
1. Core Technology Stack: Kachina Protocol and Halo2 Proof System
Through relevant information, it is found that Midnight operates based on the Kachina protocol, which divides the state of smart contracts into 'public state' and 'private state'.
Halo2 zk-SNARKs: Compared to earlier technologies, Halo2 introduces recursive proofs and does not require a trusted setup. According to real-world data from the end of 2025, Midnight has reduced verification time from 12ms to 6ms, significantly enhancing the throughput of privacy transactions.
Compact Programming Language: Developers can write privacy logic in a TypeScript-like language without needing to deeply understand the underlying cryptography. This has lowered the development threshold for 'secret smart contracts' by over 70%.
2. Unique 'Capital-Resource' Dual Token Model
Midnight's tokenomics design is the most forward-looking part of its architecture:

$NIGHT (Public Governance Token): The total supply is fixed at 24 billion. As a non-private asset, NIGHT is responsible for consensus staking and governance, and its transparency allows it to smoothly enter compliant exchanges and institutional custody systems.
DUST (Privacy Consumption Resource): DUST is non-transferable and is automatically generated by holding NIGHT. It behaves like a 'battery' that regenerates over time after consumption.
Data Insights: This design effectively balances network usage costs. As of February 2026, the daily turnover rate of NIGHT is about 1.2%, but the number of calls for DUST is growing exponentially. Since DUST is not tradable, it avoids the legal risks of privacy payments at the AML (Anti-Money Laundering) level.
II. Trend Analysis of Privacy Token Track
Today, the privacy track is no longer synonymous with 'dark web transfers' but is becoming the 'privacy infrastructure layer' of Web3.
1. Market Size and Capital Flow
According to the latest industry report, the market size of zero-knowledge proofs (ZKP) has grown from $1.28 billion in 2024 to an estimated $3.5 billion in 2026, with a compound annual growth rate (CAGR) as high as 22%.
TVL Concentration: The total locked value (TVL) of ZK projects in 2025 exceeded $28 billion.
Financing Scale: Midnight received over $100 million in R&D funding from IOG, with no early external venture capital. This 'pure' startup model is becoming the new standard for quality projects in 2026, aiming to reduce token pressure risk.
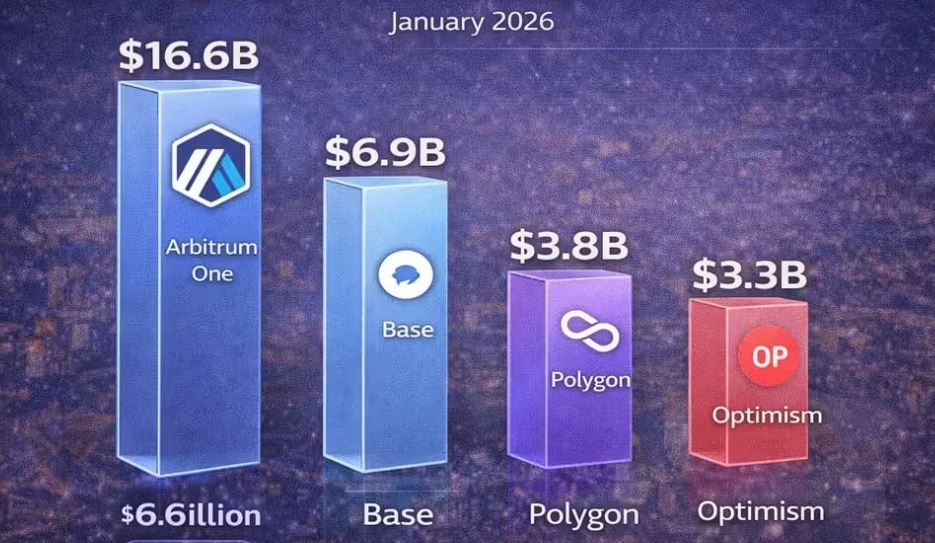
Top Project Locked Value - As of January 2026
2. Supply Distribution and Chip Structure
For example, $NIGHT has a Glacier Drop distribution covering over 8 million independent addresses.
Chip Transparency: Currently, the actual circulation of NIGHT is about 16.9% of the total, while 69.2% is still in the phased release period. This long-cycle release mechanism (450 days) aims to smooth market fluctuations, reflecting the transformation of the privacy track from 'short-term speculation' to 'long-term construction'.
III. Analysis of Future Three Development Trends
1. Transition from 'Black Box Privacy' to 'Selective Disclosure'
Future privacy projects must possess 'auditability'. Midnight supports key viewing, allowing users to provide legitimacy proof of specific transactions to regulatory authorities while protecting privacy.
Trend: Privacy coins that cannot provide selective disclosure functionality will further disappear from mainstream exchanges after 2026, while privacy layers with 'compliance access' capabilities will attract institutional funds.
2. Privacy as a Service
Privacy will no longer exist as a standalone public chain but as a cross-chain plugin. Midnight plans to provide privacy logic for applications on Ethereum and Solana chains through Layer0 integration.
Trend: 'Plug-and-Play Privacy' will become mainstream. Users do not need to migrate assets but can complete encryption operations by calling the ZK verification service of the privacy layer.
3. Explosion of Enterprise and RWA Privacy Needs
With the large-scale on-chain transformation of RWA (Real World Assets) in 2025-2026, the demand for protection of sensitive business data (such as holdings, supply chain prices, and medical records) has surged.
ZK-KYC Market: It is expected to grow to $900 million by 2032. Midnight's programmable privacy architecture perfectly fits this high-value niche market.

IV. Conclusion
The emergence of Midnight ($NIGHT) marks the entry of the privacy token track into the **'Rational Privacy'** era. By deconstructing its NIGHT/DUST dual model and ZK technology stack, we see that the core competition in the future privacy track is no longer 'who hides deeper' but 'who can find the best balance between compliance, performance, and privacy.'
For investors and developers, 2026 will be a key year for privacy infrastructure to transition from 'laboratory' to 'production environment'. In today's awakened awareness of data sovereignty, projects like Midnight, which have a strong engineering background and clear compliance pathways, are highly likely to define the Web3 security benchmark for the next five years.