Trust Wallet adds instant protection against address poisoning scams

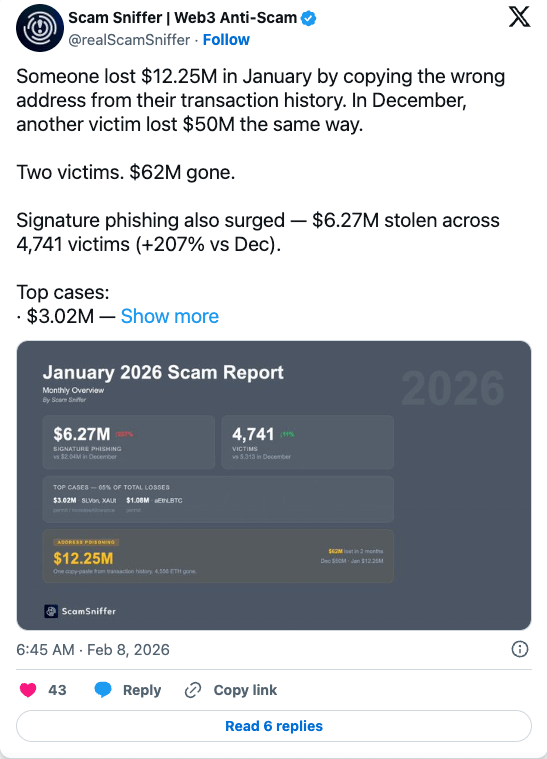
One address poisoning incident in January resulted in approximately $12.2 million after a user copied a fake address that resembled the original address from their transaction history.
This incident was followed by another major incident in December, in which almost the same trick resulted in the theft of approximately $50 million.
It's time to put an end to these incidents, isn't it?
Trust Wallet agrees. The company has launched a new feature called Address Poisoning Protection designed to detect one of the most common forms of social media fraud in the cryptocurrency space before any transaction is sent.
The scam that doesn't steal your keys
Poisoning headlines is a simple but effective attack.
Attackers send extremely small transactions, almost zero in value, to a wallet from an address that closely resembles one the victim has used previously. The fake address then appears in the user's transaction history.
When a user resends their money and copies the destination address from their history or clipboard, they may mistakenly choose the attacker's address instead of the real one.
Instead of using malware or phishing to steal private keys, the attack relies entirely on visual similarity and the user's routine habits.
Check for similar addresses before sending money
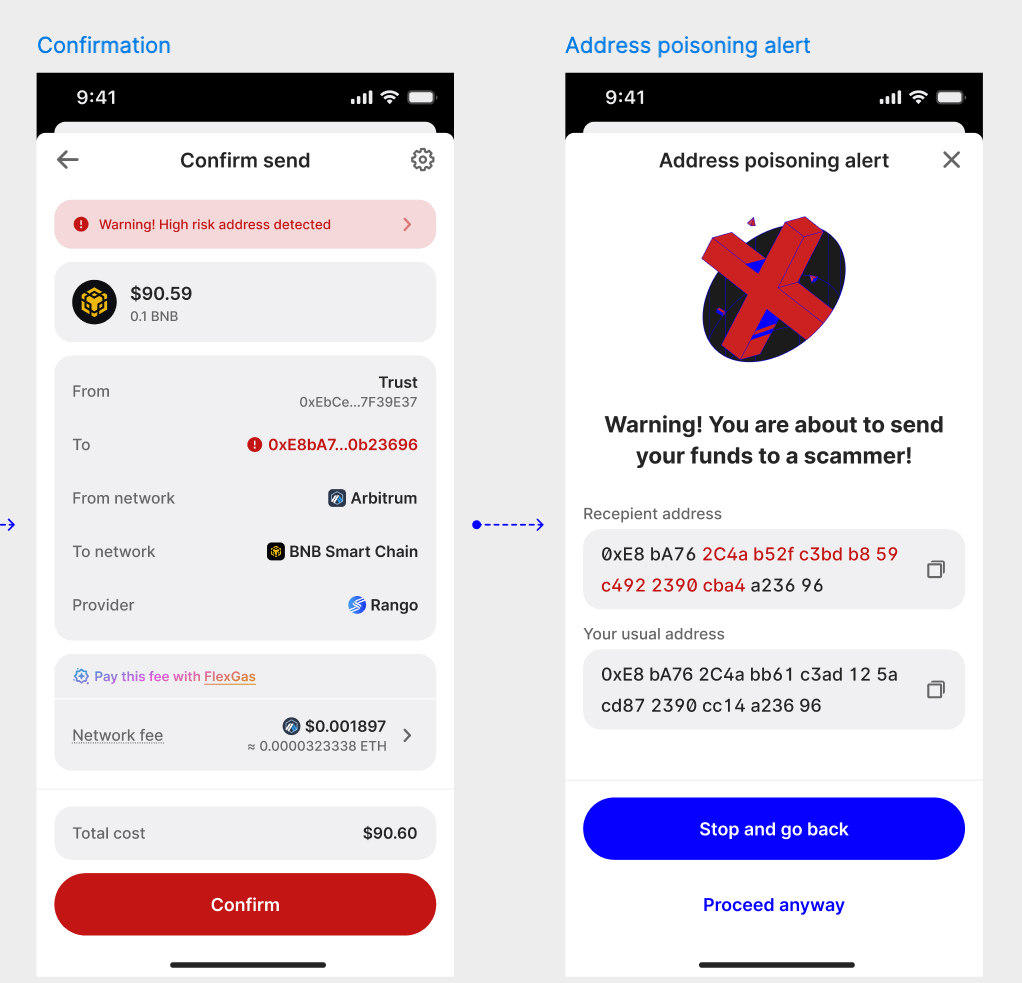
Trust Wallet’s new protection feature focuses on the moment the user enters or pastes the destination address.
When an address is copied into the submission field, the application performs a real-time scan to compare it to known phishing patterns and similar suspicious addresses. If the system detects an address that closely resembles one the user has interacted with previously, the application issues a warning.
The feature also displays a side-by-side comparison of addresses, clearly showing where each character differs. This allows users to quickly verify the legitimacy of the destination before signing the transaction.
These checks work automatically across all supported networks and are designed to operate within the normal money transfer workflow, so users do not need to manually activate any additional security settings.
Moving beyond fixed fraud lists
Many wallets already rely on blacklists of known malicious addresses. The challenge is that phishing attacks often target newly created addresses that haven't yet been flagged.
Trust Wallet's approach utilizes real-time intelligence sources rather than relying solely on static databases. The system integrates security data from HashDit and Binance Security with Trust Wallet's own monitoring tools.
This allows the wallet to detect patterns that indicate identity theft attempts, rather than just blocking reported addresses.
The protection is activated before the transaction is signed, and this is important because transactions on the blockchain cannot be undone once confirmed.
Trust Wallet has an additional share in its quiver
Address poisoning protection expands the security framework that Trust Wallet has been building over the past few years.
In 2023, the company launched a security checker, a feature designed to analyze transactions before approval. The tool scans the transaction payload itself, identifying phishing contracts, malicious applications, suspicious token approvals, and other high-risk activities.
Since its launch, the security check tool has helped prevent significant losses. Trust Wallet says the system blocked over $458 million in access to malicious contracts, helped recover over $2 million in stolen funds, and blocked $191 million in fraudulent transactions in 2025 alone.
The new poisoning protection feature addresses a different stage of the treatment process.
The security check focuses on what the user signs and analyzes the transaction payload to look for malicious behavior. Address poisoning protection focuses on who the user is sending money to and detects spoofing attempts even before the transaction is created.
Together, the two systems form a layered defense model designed to capture both technological exploits and fraud targeting humans.
Protecting users from the simplest attacks
Many of the most successful attacks today do not rely on exploiting smart contracts or breaking encryption. Instead, they target user behavior.
Address poisoning falls into this category. It exploits routine practices such as copying addresses from the transaction log or assuming the validity of familiar-looking strings.
Tools that detect these patterns early may help prevent a growing class of losses.
The latest Trust Wallet updates reflect this shift in security priorities. Protecting users today now includes detecting the subtle tricks attackers use to exploit everyday wallet behavior.