According to the 2024 Blockchain Security and Anti-Money Laundering Annual Report released by SlowMist, a total of 410 security incidents occurred in 2024, causing losses of US$2.013 billion, a decrease of 19.02% from last year. The report states:
The DeFi sector was the hardest hit, with a total of 339 security incidents, accounting for 82.68% of the total, and the loss was US$1.029 billion, a year-on-year increase of 33.12%.
Contract vulnerabilities led to 99 incidents, resulting in losses of $214 million.
There were 58 rug pull incidents with losses totaling $106 million.
Losses from wallet phishing attacks reached $494 million, up 67% year-over-year.
Faced with the severe Web3 security situation, WEEX Exchange not only strengthens its own security protection to ensure the safety of user assets, but also continues to publish a series of articles on security and anti-fraud to help users identify potential risks in the cryptocurrency field and provide best practices for protecting asset security. These measures reflect WEEX Exchange's commitment to user security and demonstrate its determination to protect the cryptocurrency community from fraud. This article selects important content from WEEX Exchange's series of articles on security and anti-fraud.
Beware of the project's "carpet pulling" scam
The term "pull the rug out" comes from the English "pull the rug out". In the field of cryptocurrency, it refers to the development team suddenly withdrawing all liquidity support after launching a new project, leaving unsuspecting investors with worthless tokens. Such scams are particularly common in DeFi projects, and many investors (both new and old) have suffered similar frauds.
A typical "carpet pull" scam usually starts with the creation of a new token and listing it on a decentralized exchange (DEX), where it is paired with valuable assets (such as ETH or SOL) and placed in a liquidity pool. Sometimes, the development team will also create hype through promotion by big Vs or KOLs. Once liquidity accumulates, the scammers will quickly withdraw all valuable assets (such as ETH) and then run away.
After an Initial DEX Offering (IDO), developers may also perform other "rug pulls" such as causing the token price to quickly drop to zero by selling a large number of tokens at once, or leaving backdoors in the contract to restrict anyone except a few addresses from selling tokens, as was the case with the infamous SQUID token scam.
According to the SlowMist report, a total of 58 "carpet pull" scams occurred in 2024, causing investors to lose $106 million.
How to identify the risks of "carpet pulling" scams?
Potential "rug pull" scams often have the following characteristics:
Lack of liquidity lock-in: No developer guarantees.
Unusual social media hype: heavily promoted by unknown or anonymous KOLs.
TVL (total value locked) is extremely low: vulnerable to price manipulation.
Vague white papers: lacking in technical details and substance.
Obvious whales: A small number of addresses holding large amounts of tokens.
To avoid falling victim to such scams, WEEX recommends that users learn more about the project before investing, conduct due diligence on the development team if necessary, and choose to trade on trusted centralized exchanges such as WEEX.
Beware of phishing scams
Have you ever clicked on a link to a cryptocurrency exchange or wallet that looked familiar? Or downloaded something that claimed to be an update?
If so, you may have fallen for a phishing scam.
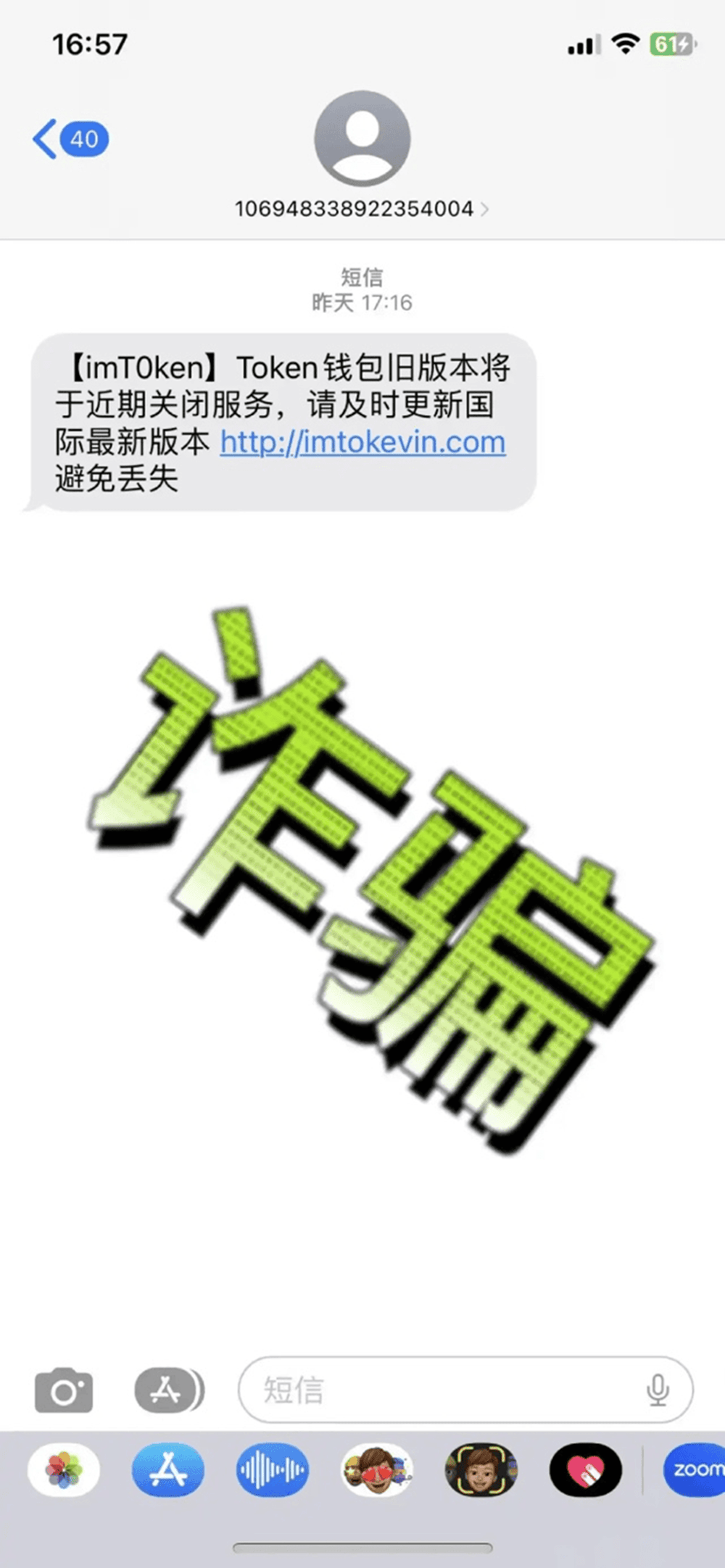
Phishing scams are fraudulent methods used by cybercriminals to obtain sensitive user information. These attackers pretend to be a trusted organization and send fraudulent messages via email, fake websites, or even via phone or text messages in order to steal your credentials or financial information.
These scams usually send you to fake websites with links that look almost identical to the real ones. Once you enter your personal information, you are deceived. Some software even prompts you to download updates, but in fact they contain malware.
Common types of phishing scams
Phishing scams are one of the main threats in the cryptocurrency space, and the WEEX exchange’s anti-phishing guide outlines how these scams work and how to identify them:
Email fraud: fake logos, urgent password reset requests, or fake promotions.
Spear phishing: This scam is often customized using the victim’s personal information (such as name, social media activity, etc.) to conduct personalized fraud.
Voice phishing: Fake phone calls impersonating customer service.
SMS phishing: SMS scams related to fake security vulnerabilities or airdrops.
How to protect yourself from phishing scams?
WEEX has always reminded users to remember the official website. If they encounter any unknown links, or Telegram, WeChat, QQ numbers, emails, etc. claiming to be customer service personnel, they must verify them through official verification channels or confirm with WEEX global community staff.
When downloading and installing the WEEX App, please be sure to download it through official channels, or search for "WEEX" in the App Store/Google Play official store to install it. Avoid downloading any apps from unknown sources or clicking on unknown links.
In addition, you can also fill in the anti-phishing code in the security settings of your WEEX account to ensure that all official emails you receive contain the code. If the code is not in the email, it may be a phishing email.
Other common cryptocurrency scams
WEEX Exchange’s security and anti-fraud series also introduces other common scams such as hacker attacks, fake ICO/IEO, pump and dump, etc.:
Hacker attacks: Cryptocurrency exchanges and wallets are often targeted by hackers. To prevent your account from being hacked, users are advised to use strong passwords and enable two-factor authentication (2FA).
Fake ICO/IEO scams: These financing methods can be exploited by scammers who promote fraudulent projects through fake websites or social media. Users must conduct a comprehensive background check on the project and team before investing.
Pump and dump scam: By manipulating market prices to attract investors, the tokens are eventually sold on a large scale, causing prices to plummet and investors to suffer heavy losses.
Ponzi scheme: This scam uses high returns as bait, but in practice it uses the money of subsequent investors to pay the returns of previous investors, which eventually leads to a break in the capital chain and investors lose all their money.

How to choose a trustworthy trading platform?
After learning about these cryptocurrency scams, it is particularly important to choose a safe and reliable trading platform, because if you choose a scam platform, you may lose a lot of money; and if you choose an unreliable platform, you may face the risk of losing all your assets.
Cryptocurrency trading platforms are mainly divided into centralized trading platforms (CEX) and decentralized trading platforms (DEX). For most users, they need to pay special attention to the following key factors when choosing a CEX platform:
Safety measures:
Two-Factor Authentication (2FA): Make sure the exchange offers 2FA for increased account security.
Encryption & Cold Storage: Verify that the exchange uses strong encryption and extensive cold storage to protect assets.
Risk control systems: Ensure that exchanges have mechanisms in place to detect and respond to suspicious activities in real time.
Proof of Reserves: Exchanges should provide verifiable proof of reserves to ensure their financial stability.
Protection Fund: The exchange should set up a user asset protection fund. WEEX Exchange has established an investor protection fund of 1,000 BTC since its establishment.
History:
Security incident history: Check whether the exchange has had any security incidents in the past and how they were handled.
Continuous improvement: Is the exchange constantly updating its security measures?
Customer Service:
A complete customer service system that can quickly respond to user questions. WEEX provides 24-hour multilingual customer service support.
User reviews and community trust:
Community Feedback: Read user reviews to learn about the exchange’s security and customer service.
Participate in discussions: actively communicate with the community to build trust and transparency.
Conclusion
In the crypto world full of opportunities and challenges, it is vital to remain vigilant and enhance self-protection awareness. By deeply researching projects, choosing trustworthy trading platforms, and being sensitive to security threats, we can effectively reduce the risk of becoming a victim of fraud. Let us work together to build a more secure and transparent Web3 ecosystem.