Hey Binance Square crew, If you've been sleeping on SIGN, this might be the post that wakes you up. We're talking about something that's not just another DeFi gimmick or meme coin pump—it's the infrastructure layer governments are actually using to go on-chain in 2026. Fresh off the March 20 mainnet update, Sign Protocol just dropped Sign-Scan V2 and doubled down on their S.I.G.N. sovereign framework. This isn't hype from some Twitter thread; I've been digging into the docs, partnerships, and real deployments for weeks. Buckle up—this is gonna be long, detailed, and 100% my raw take. Zero fluff, all signal.
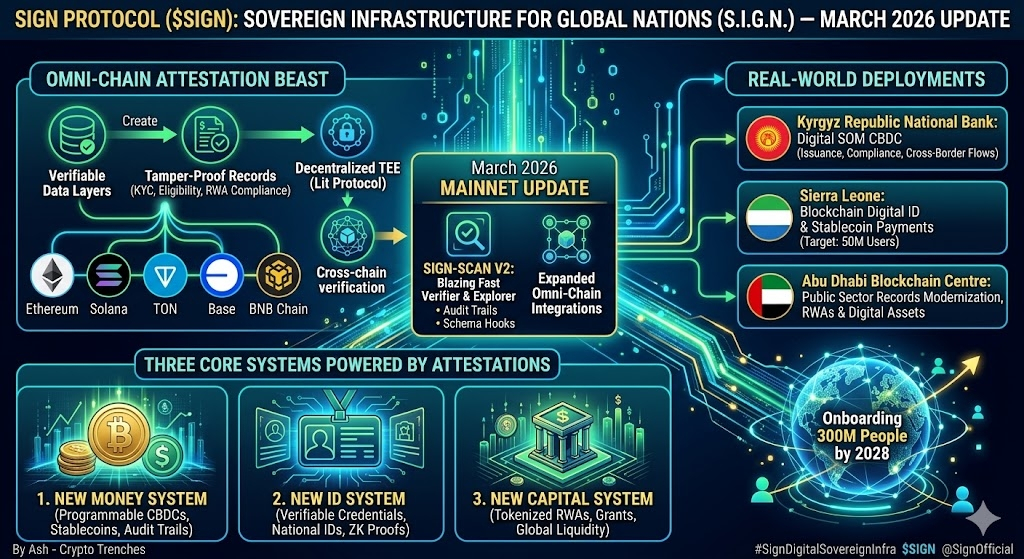
First off, let's set the scene. We've all seen the "blockchain for good" talk since 2017. Governments dip their toes with CBDCs or digital IDs, but it always hits the same wall: how do you make data verifiable, cross-chain, private, and audit-proof without handing everything to a central database or locking it to one chain? Enter Sign Protocol—the omni-chain attestation beast that's now the evidence layer for entire national systems.

For the newbies: Sign Protocol lets anyone (devs, DAOs, or freaking governments) create "attestations"—tamper-proof, cryptographically signed records of facts. Think "this wallet passed KYC," "this citizen is eligible for benefits," or "this RWA was tokenized with full compliance." Schemas define the structure, attestations are the signed data (on-chain or hybrid with Arweave/IPFS for big files), and everything is verifiable across Ethereum, Solana, TON, Base, you name it. No single chain owns the truth. That's the omni-chain magic.
But here's the fresh 2026 subject everyone's sleeping on: the full S.I.G.N. rollout (Sovereign Infrastructure for Global Nations) and the March mainnet update with Sign-Scan V2. This isn't incremental. It's the protocol going from "cool Web3 tool" to the backbone of real sovereign digital economies. Docs just reframed everything around three core systems:

New Money System – Programmable CBDCs and stablecoins with built-in policy controls, oversight, and audit trails via attestations. No more black-box central bank experiments.
New ID System – Verifiable credentials and national digital IDs with privacy-preserving ZK proofs. Citizens prove stuff (age, eligibility, ownership) without exposing raw data.
New Capital System – Tokenized RWAs, grants, benefits, and programmable capital markets. Think commodities or resources from resource-rich nations hitting global liquidity with full traceability.
Sign Protocol isn't building the chains themselves—it's the shared "inspection-ready evidence layer" that makes all three work together seamlessly. Attestations created on a private sovereign rail can unlock vesting on public chains, verify identities across borders, or settle CBDC payments. Cross-chain verification? Handled via decentralized TEEs (partnered with Lit Protocol) so no custom bridges needed. Mind-blowing composability.
Let me start with the basics so we’re all on the same page. Sign Protocol itself isn’t a blockchain. It’s the layer that lets anyone create “attestations” – basically signed, structured proofs of facts. You define a schema (like a template: “User passed KYC on this date with these details”), someone attests to it (signs it cryptographically), and then anyone can verify it later across chains. Data can sit on public chains like Ethereum, Solana, Base, or even private/sovereign setups, with bigger files on Arweave or IPFS for permanence. Privacy options include encryption and ZK proofs so you don’t leak everything.
Sign-Scan has always been the “see and search” part of this. Before V2 it was functional but felt a bit scattered – you could browse attestations, but switching chains or digging deep required jumping around. The March 2026 mainnet update rolled out Sign-Scan V2 as the unified hub. It’s now the single place where everything aggregates: attestations from multiple chains, hybrid storage, private rails if needed, and it ties directly into the bigger S.I.G.N. vision for national money, ID, and capital systems.
What Hit in V2 That Feels Fresh
From what I saw playing with it:
Unified View Across Everything: You no longer hunt for attestations chain-by-chain. V2 pulls in data from supported EVM chains, and whatever sovereign setups are anchored. I searched a public schema and instantly saw attestations from different networks in one feed. The explorer shows filters for network, attester address, subject (the wallet or entity being attested about), timestamp, and even custom fields inside the schema. For big national stuff like digital IDs or CBDC issuances, this means auditors or citizens can check records without needing separate tools per chain.
Faster, Smoother Explorer for Normal People: The UI at scan.sign.global got cleaner. Recommended schemas pop up first, you can browse “All Type” or filter quickly. I clicked around and saw visual overviews – total attestations per schema, creation dates, who issued them. Non-devs (think government officials or regular users verifying their own credentials) can actually navigate without coding. It’s not flashy like some meme dashboards, but it’s practical and loads quick even with thousands of entries.
Real Developer Power – REST + GraphQL APIs: This is where V2 shines if you’re building. The docs lay out clean endpoints for fetching specific attestations, batch pulls, or complex filters. GraphQL lets you ask precisely what you want – like “give me all attestations under Schema XYZ from this attester after March 1, only those with ZK proof enabled.” I didn’t spin up a full app, but the examples made sense for integrating into a frontend dashboard or backend compliance checker. SDK patterns help too, so you’re not fighting raw HTTP calls. Builders can now query at national scale without building their own indexer from scratch.
Tighter Hook Integration: Schema Hooks (those smart contracts that fire on every new attestation or revocation) now feel first-class in V2. When a hook runs – say, to whitelist someone or trigger a payment – the resulting data gets indexed nicely so you can see and query the effects right away in Sign-Scan. I read the workshop-style examples; one simple whitelist hook restricts who can attest, another could gate access or notify contracts. In a sovereign context, this means policy rules (like “only approved banks can issue CBDC attestations”) can run automatically, and the audit trail stays visible and verifiable.
Sovereign and Privacy Upgrades: V2 handles hybrid/public/private attestations better. For governments using private rails (like in the Kyrgyz Digital SOM CBDC pilot or Sierra Leone’s digital ID MoU), attestations can stay controlled but still get verified publicly when needed – via decentralized TEEs with Lit Protocol partners for cross-chain trust (2/3+ threshold signatures). ZK selective disclosure means you prove “I’m eligible” without showing full details. Audit trails are inspection-ready, which fits the “New Money, New ID, New Capital” pillars of S.I.G.N. perfectly.
I also noticed performance tweaks for handling millions of attestations – important when a country rolls out national IDs or token distributions at scale. They’ve already moved billions in assets historically through related tools like TokenTable, so the indexing needs to keep up.
How It Ties Into Real Stuff Happening Now
In practice, this V2 explorer becomes useful for the partnerships we’ve seen:
Kyrgyz Republic’s National Bank using attestations for Digital SOM CBDC compliance and flows.
Sierra Leone’s MoU for blockchain-based digital ID and stablecoin payments – transparency without central data hoarding.
Abu Dhabi Blockchain Centre collaboration for public sector records and sovereign RWAs, with plans for a dedicated office.
Sign-Scan V2 lets officials, devs, or even citizens query these attestations in one place. No more “where’s my record?” headaches. For DeFi builders, it means better sybil resistance, merit-based airdrops, or compliant RWAs where anyone can verify provenance instantly.
My Honest Frustrations and Wins
Frustrations first: Docs are still a bit high-level on exact V2 changelog diffs – they focus more on the overall S.I.G.N. framing. Some advanced cross-chain examples assume you already know the older setup. I had to piece things together from the explorer, FAQ, and builder sections. Testnet version (testnet-scan.sign.global) is handy to experiment without real gas.
Wins: Once I created a dummy schema and attested via the app.sign.global dashboard (no-code option exists!), seeing it appear in the explorer felt satisfying. The GraphQL playground (implied in docs) makes testing queries easy. For someone like me who’s not a full-time Solidity dev, the balance between power and usability is decent.
Compared to lighter attestation tools out there, V2 emphasizes scale, hybrid storage, sovereign control, and programmable hooks. It’s not trying to be the prettiest UI – it’s trying to be the reliable backbone.
Quick Tips If You Want to Try It Yourself
Go to scan.sign.global – browse recommended schemas or search by address.
Check docs.sign.global For Builders for API examples and Schema Hook interface.
Play on testnet first if you want to create/test attestations.
For deeper sovereign reads, look at the FAQ on S.I.G.N. architecture.
Bottom line from my digging: Sign-Scan V2 isn’t revolutionary eye candy, but it makes the whole attestation system actually usable at the scale governments need in 2026. When combined with Schema Hooks, cross-chain verification, and privacy tools, it starts feeling like real infrastructure instead of another Web3 experiment. The March update pushed it from “cool for DAOs” toward “table stakes for national digital systems.”
What about you? Have any of you opened scan.sign.global since the V2 rollout. What schema or use case would you want to see indexed better. Devs – how do the new APIs feel compared to before? Governments watchers – does this solve real audit/verification pain points for you
Drop your thoughts, questions, or even screenshots of what you found in the explorer. I’ll reply to as many as I can. Let’s turn this into a proper thread on fresh sovereign infra.
Real-world proof this is happening right now (not vaporware):
Kyrgyz Republic: National Bank partnering for Digital SOM CBDC. Attestations handle issuance, compliance, and cross-border flows.
Sierra Leone: MoU for blockchain-based digital ID + stablecoin payments. Transparency and inclusion at scale—50 million users targeted across deployments.
Abu Dhabi Blockchain Centre: Public sector records modernization. RWAs and digital assets flowing into global markets.
CEO Xin Yan has been vocal: mass adoption isn't retail memes—it's governments embedding blockchain into money, identity, and capital markets. They've already served millions and distributed billions in digital assets. Goal? Onboard 300 million people by 2028. CZ dropped $16M into their token airdrop services, and YZi Labs followed up to scale on BNB Chain. That's not random—it's big players betting on sovereign infra.
Now, the super fresh March 2026 update that dropped like a bomb: Sign-Scan V2 full rollout + expanded omni-chain integrations (Ethereum, Solana, Base, and more). Sign-Scan is their explorer/ verifier tool, and V2 makes it blazing fast for real-world data checks. Search attestations, verify credentials, audit trails—all in one place, no more clunky single-chain explorers. Paired with Schema Hooks (custom logic that triggers on attestation creation/revocation—whitelists, payments, anything), devs can build gated apps that feel enterprise-grade but stay decentralized.
Why does this matter for us retail degens and builders?
DeFi & DAOs: Attestations kill sybil attacks. Airdrops become merit-based. Reputation systems actually work cross-chain.
RWAs: Real compliance without TradFi middlemen. Governments tokenize resources; protocols verify instantly.
Privacy + Compliance: ZK modes + hybrid storage = you control your data, regulators get their proofs. Solves the "Web3 vs regulation" headache.
Mass Adoption: When a country rolls out digital IDs via Sign, that's millions of wallets interacting with attestations daily. Network effects go nuclear.
Token utility.SIGN isn't just governance (vote on upgrades, parameters, funding). It's the gas for attestations at scale, staking for verifiers, and incentives in the ecosystem. Post-airdrop in 2025, it's been volatile but the fundamentals are stacking. With sovereign deals closing, utility is about to go parabolic. Price action aside (I'm not shilling numbers—DYOR), the narrative shift from "speculation" to "sovereign infra" is real. 2026 is the year crypto stops begging for adoption and starts powering nations.
My honest take after weeks of rabbit-holing the docs and partnerships: This feels like the missing piece. We've had L1s, L2s, bridges, oracles. But trust and verifiable data? That's the final boss for real-world utility. Sign Protocol didn't just solve cross-chain attestations—they made it sovereign-ready. No single chain owns it. Privacy by default. Auditability baked in. And the timing? Perfect with macro clarity on digital assets and institutions piling into RWAs.
Risks? Sure—regulatory pushback in some countries, execution on multi-nation rollouts, or competition from EAS/Farcaster-style attestation plays. But the government MoUs and CZ backing give it legs most protocols dream of. If even one CBDC or national ID goes live at scale, sign becomes table stakes for the next bull leg.
What do you guys think. Is S.I.G.N. the next big narrative after RWAs and AI agents, or am I early? Have you messed with Sign-Scan V2 yet? Drop your attestations or thoughts below—let's discuss. If you're building or just curious, check sign.global and the docs. This is the stuff that actually moves the industry forward.
DYOR, NFA, and stay safe out there. 2026 is gonna be wild—happy attesting! 🔥
