In the world of digital identity, the conversation often centers around architecture. Centralized systems promise speed, federated systems promise coordination, and wallet-based systems promise user control. On the surface, these distinctions make it easy to debate which model is “best.” But after seeing these systems in action, it becomes clear that the real challenge isn’t architecture—it’s trust.
Centralized systems are efficient, and governments love them because rollout is straightforward and oversight is clear. But efficiency often comes at a hidden cost. A single API call can expose more data than intended—not because of a breach, but because the system was designed without careful limits. Federated systems attempt to reduce this risk, but they introduce operational friction: multiple agencies, different rules, and coordination challenges create bottlenecks that only multiply with scale. Wallet-based identity, which places credentials in the hands of users, feels right philosophically, but it comes with practical headaches: lost devices, stale credentials, and onboarding new verifiers all add hidden complexity.
What becomes clear across these models is that trade-offs are inevitable. Speed versus privacy. Control versus flexibility. Audit versus data minimization. And these compromises often only surface once a system is live—when adjustments are costly, politically sensitive, or practically impossible.
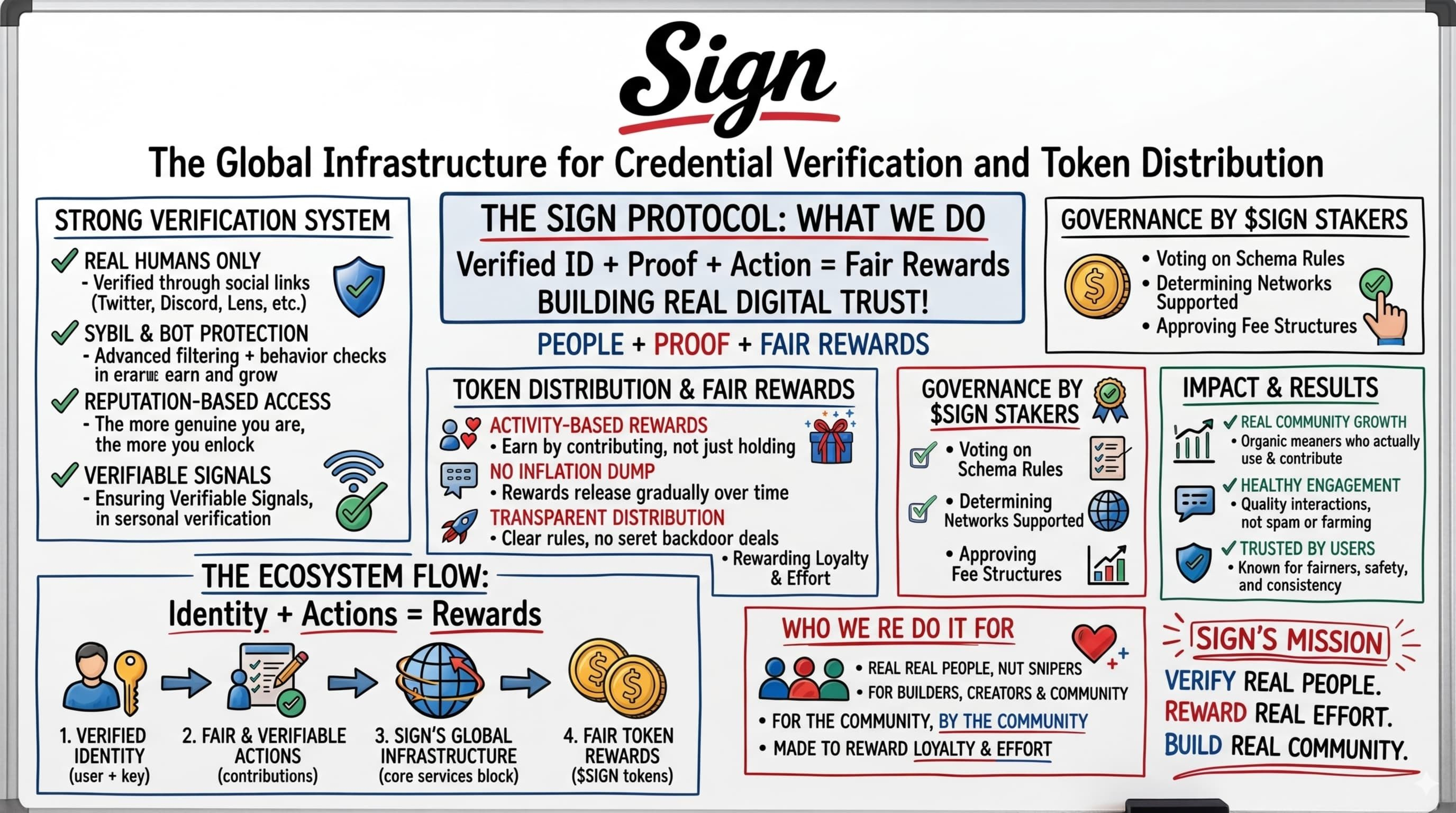
That’s why SIGN stands out. It doesn’t try to replace existing identity systems. It works beneath them, focusing on the trust layer: the part that decides who can issue credentials, what gets shared, how it’s verified, and whether it holds up under scrutiny. Trust is rarely the flashy part of a system, but it’s the part that usually breaks. SIGN tackles this head-on.
Issuer authority is explicit and governed, not assumed. This matters because even one weak issuer can undermine an entire network. Data exposure is minimized by design, using proofs rather than raw records to prevent accidental leakage. Revocation is taken seriously: if credentials can’t be invalidated reliably, trust collapses. SIGN designs for real-world conditions, including offline scenarios. Audit balances transparency and privacy, allowing verifiable actions without exposing unnecessary user data.
The result is infrastructure that isn’t flashy or immediately celebrated—but if it works, it becomes indispensable. History shows that the layers handling identity, verification, and settlement often go unnoticed until failure becomes costly. Good infrastructure is invisible; bad infrastructure dominates headlines.
SIGN’s approach also reflects a pragmatic reality: no single identity model will dominate indefinitely. Countries will mix centralized, federated, and wallet-based solutions. Without a robust trust layer, all approaches suffer the same fate: overexposure, governance gaps, and unreliable audit trails. By addressing these challenges early, SIGN positions itself as foundational, not transient.
Yet even as SIGN addresses technical trust, it also navigates subtle human dynamics. The protocol allows credentials to flow across platforms, reducing friction and enabling portability. But this efficiency depends on trust in validators. Even in a decentralized network, norms and biases could influence which credentials are recognized, subtly shaping control while claiming neutrality. There’s a delicate balance between enabling freedom and inadvertently reinforcing hierarchy, and that tension is built into the system in ways that are fascinating and consequential.
Privacy and transparency also demand compromise. Validators must see some level of data to verify authenticity, but this introduces tension: how much visibility is necessary, and how much undermines user privacy? These trade-offs may not be obvious to everyday users, but they define the protocol’s integrity and resilience. Technical elegance alone doesn’t guarantee real-world adoption—human behavior, institutional pressures, and regulatory frameworks create friction that no specification can fully anticipate.
Beyond trust and protocol mechanics, SIGN introduces an intriguing behavioral dimension through its Orange Basic Income program, or OBI. This isn’t a simple airdrop or marketing stunt. The OBI represents a social contract encoded in smart contracts, where users holding assets on-chain can receive rewards based on participation, not just accumulation. The emphasis is on duration and consistent engagement: holding tokens in a self-custody wallet earns more than simply buying and selling quickly. By requiring wallets outside centralized exchanges, the protocol ensures transparency and on-chain accountability.
OBI also encourages collective engagement. When network activity or attestation milestones are met, additional rewards are unlocked for all participants. This approach fosters real utility, not mere hype. Users are incentivized to interact meaningfully with the protocol, turning theoretical value into functional adoption. Unlike traditional airdrops, which often reward short-term speculation, OBI rewards genuine, sustained participation, aligning economic incentives with long-term network health.
Of course, there are limits. While 100 million $SIGN tokens may seem substantial, widespread participation dilutes rewards. The protocol’s designers are aware of this and plan to adjust strategies in future seasons, offering “boosts” for early and engaged users. Success depends on ongoing monitoring and authentic engagement. Those who chase rewards without interacting meaningfully may find themselves sidelined. The real test is whether behavior aligns with natural usage rather than gaming the system.
Ultimately, SIGN represents more than a protocol or a product. It’s an experiment in digitally formalizing trust while preserving flexibility, privacy, and resilience. It demonstrates that infrastructure doesn’t need hype to be valuable—it needs stability, reliability, and careful attention to human and systemic behavior. Its real impact may go unnoticed at first, but over time, foundational trust will prove more consequential than any flashy feature.
SIGN’s approach is subtle yet profound: it shapes identity and verification without imposing a rigid model, rewards meaningful participation, and addresses the operational realities that most systems ignore. If it succeeds, it may set a template for future digital identity systems, blending technology and human behavior into a coherent, resilient ecosystem. And if it fails, it will be a reminder that trust is harder to codify than code. Either way, observing SIGN’s journey offers insights into the future of digital sovereignty, proving that in identity, the invisible foundations are always the ones that matter most.
@SignOfficial #SignDigitalSovereignInfra $SIGN
