I used to think once identity is verified, the system should be done with it. But the moment you try to reuse that verification, the system quietly resets.
You go through a proper check. Passport scanned, data validated, everything matches. High assurance, strong standards, nothing questionable. That part is already solved.
Then you move forward and get asked again.
Not because something failed. Because nothing carried forward.
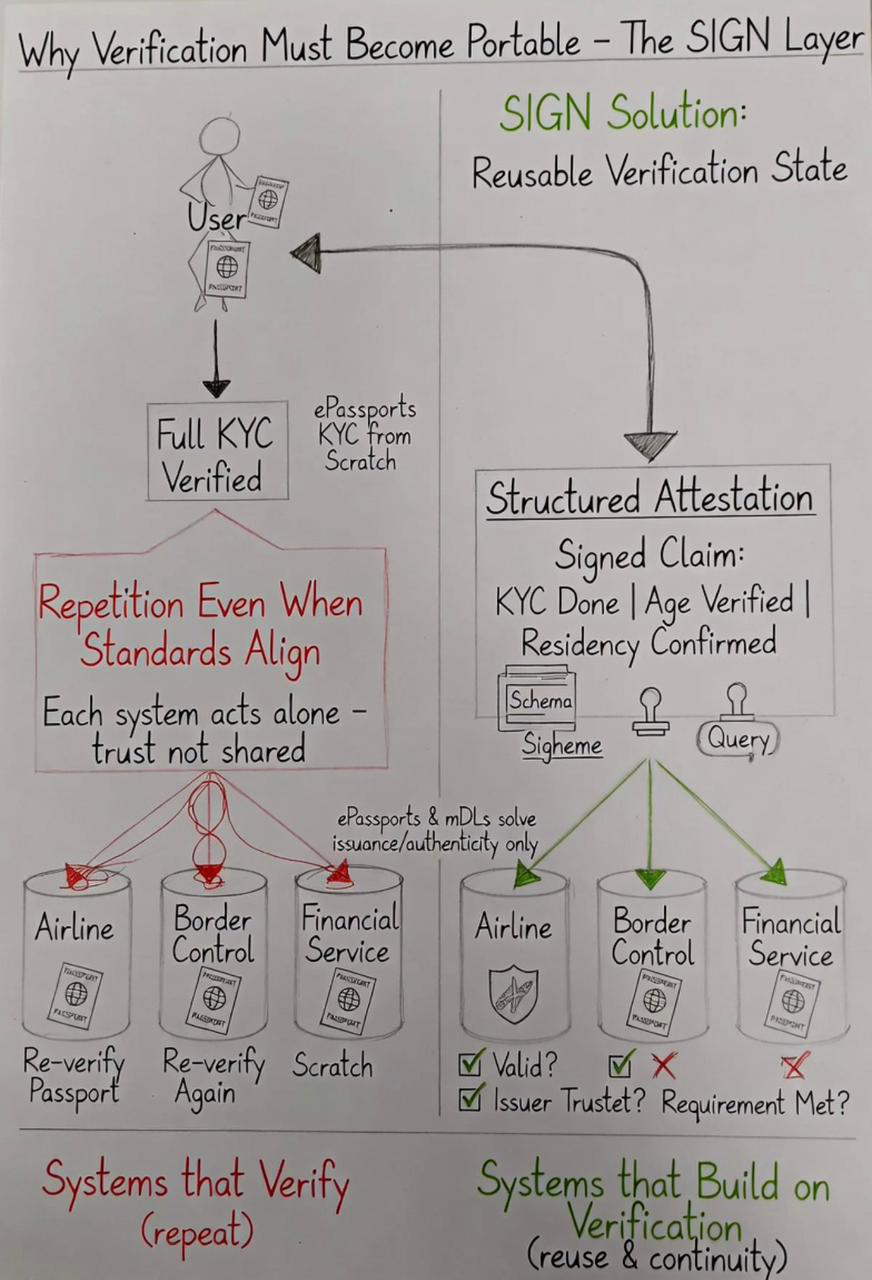
I’ve seen this play out in a very specific way. A user completes full KYC through a regulated provider. Document verified, liveness checked, compliance rules satisfied. That result is accepted inside that system.
Then the same user tries to access another regulated service.
They get asked to do KYC again.
Same jurisdiction. Same type of requirements. Sometimes even overlapping compliance frameworks. But the second system doesn’t rely on the first result. It restarts the process.
Now scale that.
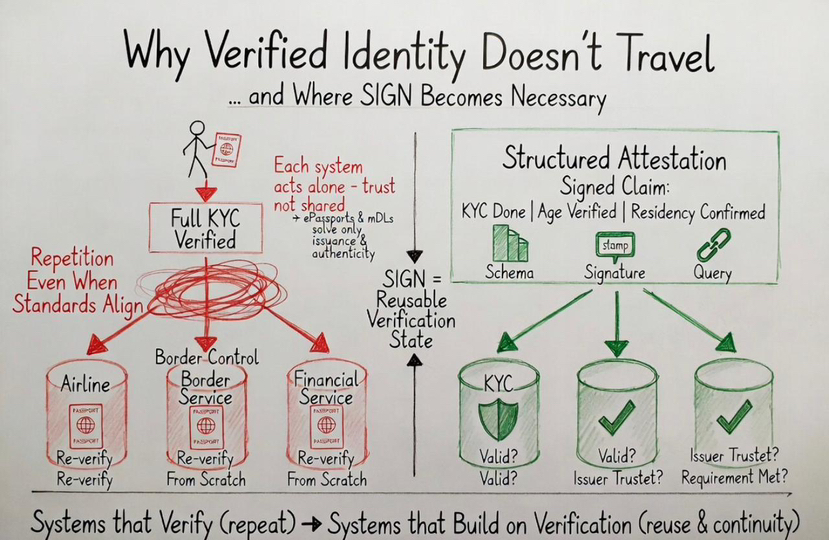
Airline verifies identity using passport data. Border system verifies again under its own logic. Financial service runs KYC separately.
Each one is technically correct.
But the system behaves like each of them exists alone.
That’s where the problem actually sits.
Not in identity. Not in verification.
In the fact that verification results don’t move.
ePassports and mDLs are often treated as the solution layer. They’re not.
They solve something very specific and they solve it well.
They define: who issued the identity how it is structured how authenticity is checked
They do not define: how one system should trust another system’s verification result how verification outcomes are expressed how those outcomes persist across boundaries
So every system ends up doing the same thing again.
Not because it needs to verify identity. Because it cannot rely on someone else’s verification.
That’s why repetition exists even when standards are aligned.
Standards align inputs. They don’t align outcomes.
At scale, systems don’t disagree because data is wrong. They disagree because trust isn’t shared.
And when trust isn’t shared, every system is forced to recreate it.
This is where SIGN stops looking like an add-on and starts looking like a missing layer.
Because the system doesn’t need stronger identity at this point.
It needs reusable verification state.
What SIGN does is not “store identity” or “replace credentials”.
It captures what happened after verification and makes it portable.
Once identity is verified using a passport or mDL, that result is turned into a structured attestation.
Not raw identity again.
A claim about what has already been confirmed.
KYC completed under a defined standard. Age verified above a threshold. Residency confirmed under a specific issuer.
That claim is tied to a schema so its meaning cannot drift. It is signed by the issuer so responsibility is clear. It is queryable so another system can resolve it directly.
And if that verification is later revoked or updated, the status changes at the source — not silently ignored by downstream systems.
Now the next system doesn’t ask for identity again.
It evaluates:
Is this attestation valid Do I accept this issuer Does this satisfy my requirement
And this is where real system behavior shows up.
Because not every system will accept every issuer.
One regulator may recognize a KYC provider. Another may reject it.
Two valid attestations can exist for the same user… and still lead to different outcomes.
SIGN doesn’t hide that conflict.
It makes it explicit, so systems stop repeating blindly and start making their trust assumptions visible.
At scale, what breaks systems isn’t bad identity. It’s the absence of shared decisions about identity.
This is the part most people underestimate.
The system is no longer verifying identity.
It is verifying a prior decision under defined conditions.
And that changes the behavior of the entire network.
Because once decisions become portable, repetition stops being necessary.
Airline doesn’t need to re-run checks already performed under trusted conditions. Exchange doesn’t need to redo KYC if the prior verification meets its threshold. Service providers stop rebuilding trust from zero each time.
Without this layer, even perfect standards don’t scale.
You can verify identity anywhere.
You just can’t use that verification anywhere else.
And this is where systems quietly start breaking.
Not with errors.
With drift.
One system accepts a credential based on its own verification. Another system rejects the same user because it requires a different process.
Both are technically correct.
But the system as a whole becomes inconsistent.
What looks like security is often just repetition. And repetition doesn’t scale — it fragments.
SIGN doesn’t remove trust decisions.
It exposes them and makes them reusable.
Each system still decides which issuers it accepts. Each system still defines its own thresholds.
But instead of repeating verification, it can rely on structured, signed outcomes that already exist.
That’s the difference between:
systems that verify and systems that build on verification
Once you see that, compatibility with ePassport and mDL looks incomplete without this layer.
Because those systems stop at identity.
SIGN extends identity into continuity.
And that’s where the real constraint is starting to show.
Not in proving identity.
In carrying it forward.
If verification cannot move, identity does not scale. It just repeats.
And once systems start repeating the same truth differently, trust doesn’t break loudly — it splits quietly.