I have been thinking about how often I rely on single sign on systems without really noticing it. Logging into platforms through Google or other providers has become second nature. It feels convenient. Fast. Familiar. But the more I think about it the more I realize how much control sits behind that convenience. One provider manages identity access and authentication across multiple services. If that layer fails or restricts access everything built on top of it feels the impact.
That is what made me look more closely at how SignPass connected to Sign Protocol positions itself as an alternative.
At first the idea sounds compelling.
Instead of relying on a centralized provider users could authenticate using attestations. Identity credentials permissions and access rights could be verified through cryptographic proofs rather than a single authority. In theory this shifts control back to the user. Identity becomes portable rather than platform dependent.
But I remain cautious.
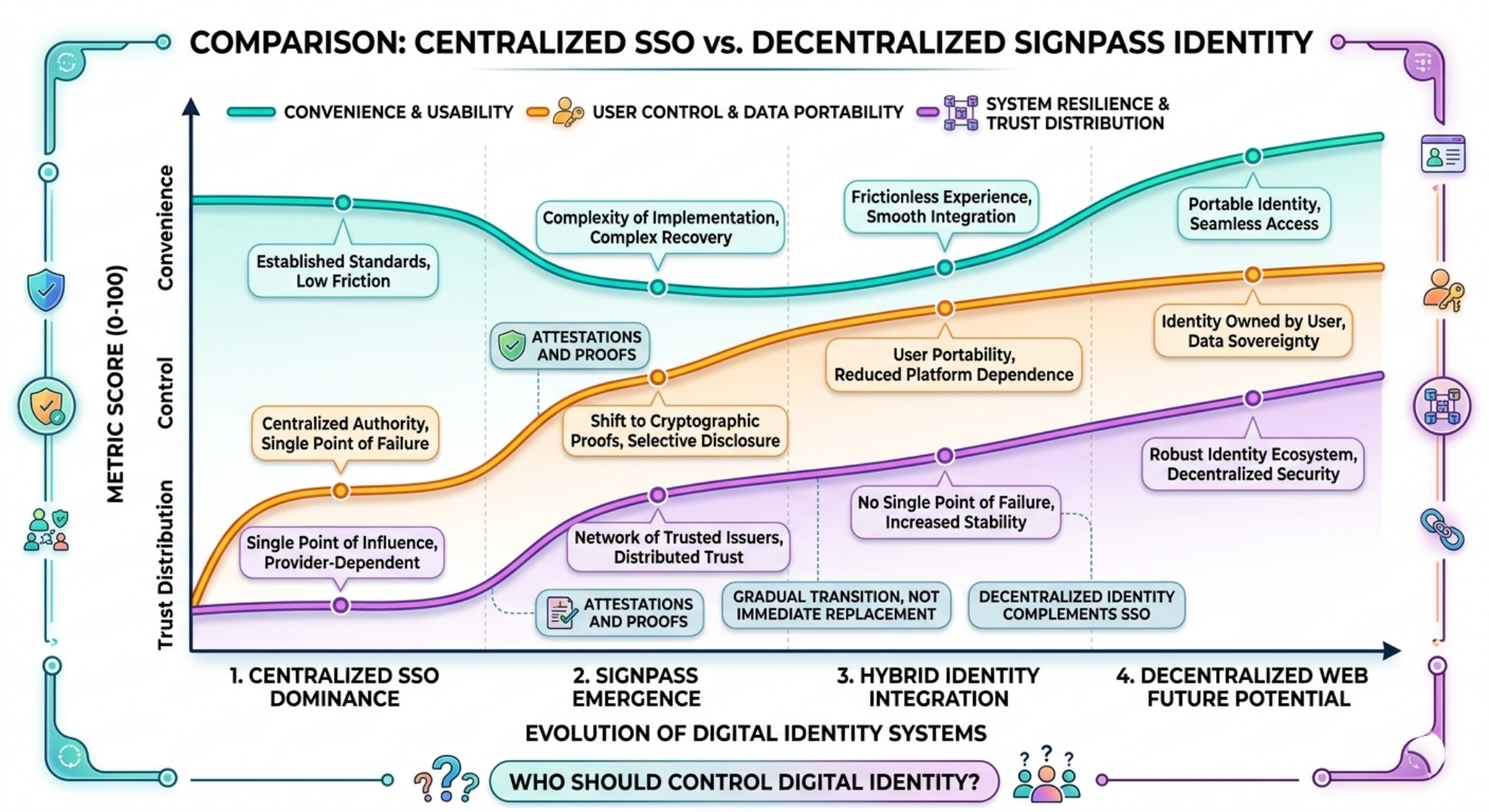
Single sign on systems exist for a reason. They reduce friction. They handle complexity in the background. They integrate easily with existing applications. Replacing them is not just about offering a different model. It requires matching or exceeding that level of usability.
From a technical perspective SignPass introduces an interesting shift.
Authentication becomes a matter of presenting a valid attestation. A user proves they meet certain conditions without necessarily revealing full identity details. This aligns with the broader idea of selective disclosure. Applications verify what they need to know and nothing more.
That sounds efficient.
But I keep coming back to trust.
In centralized SSO systems trust is placed in the provider. In a decentralized model trust shifts to issuers of attestations. If a credential is issued by a recognized authority it carries weight. If not it may be ignored. This means the system depends heavily on a network of trusted issuers rather than a single provider.
Another challenge is integration.
Most applications today are built around existing authentication standards. OAuth flows session management and identity providers are deeply embedded in current systems. For SignPass to replace SSO it must integrate with these environments without introducing significant complexity. Otherwise developers may hesitate to adopt it.
There is also the question of recovery.
Centralized providers offer account recovery mechanisms. Password resets. Multi factor authentication. Support systems. In a decentralized model recovery becomes more complex. If a user loses access to their credentials the system must provide a secure way to restore identity without compromising security.
From my perspective this is one of the harder problems to solve.
Still I can see why the idea is gaining attention.
Centralized identity systems concentrate control and data. They create single points of failure and influence. As digital systems expand users may want more control over how their identity is managed and shared.
SignPass appears to explore that direction.
It does not eliminate authentication. It changes how it is structured. Instead of logging in through a provider users present verifiable proofs that grant access. Identity becomes something carried rather than something requested.
That distinction matters.
But I am not convinced that replacement is immediate.
More likely the transition if it happens will be gradual. Hybrid systems may emerge where decentralized identity complements existing SSO rather than fully replacing it. Applications may adopt attestations for specific use cases while still relying on traditional login systems for others.
What I find interesting is that this approach challenges a deeply ingrained assumption.
That identity must be managed by a central authority.
Whether that assumption changes depends on more than technology. It depends on user behavior developer adoption and institutional acceptance.
For now I see SignPass less as a direct replacement for SSO and more as an alternative model.
One that highlights the tradeoffs between convenience control and trust.
If it succeeds it could reshape how authentication works across digital systems.
If it does not centralized providers will likely remain dominant.
Either way the question it raises is difficult to ignore.
Who should control digital identity.
And how that control should be exercised in a system that is becoming increasingly interconnected.